Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About AWS Organizations
AWS Organizations evidence includes accounts, OUs, roots, SCPs, and related policies. The role must live in the management account - member accounts cannot enumerate the full org graph via these APIs.How it works
AttachAWSOrganizationsReadOnlyAccess, or narrow to organizations:Describe* / organizations:List* via inline JSON.
| Detail | Value |
|---|---|
| Category | Cloud governance |
| Authentication | Cross-account IAM role (management account) |
Prerequisites
- IAM admin rights in the management account (not a workload member account).
- Connector principal + external ID.
Connect AWS Organizations to Iru
Copy the trust policy from Iru
Turn on AWS Organizations
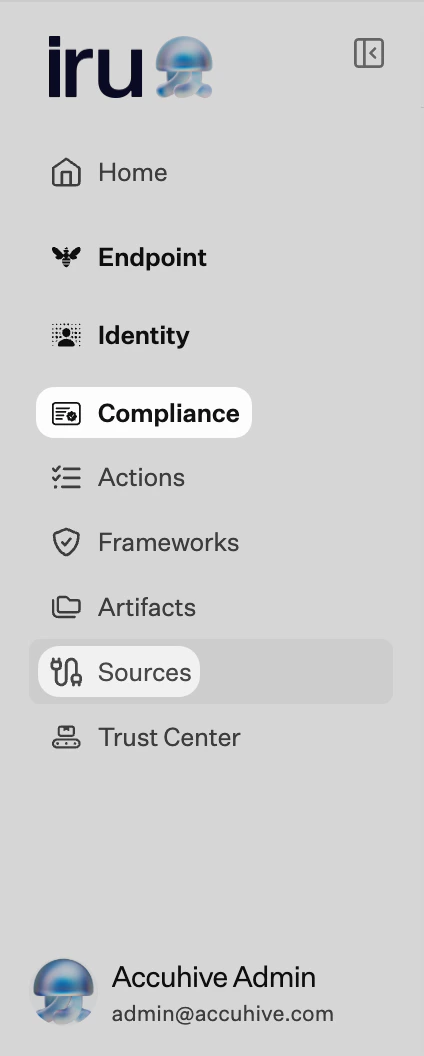
Find AWS Organizations (use Category or Search by name or description). On that card, turn on the toggle. Leave the wizard tab open.
Create the IAM role in the management account
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 (or the ID Iru shows). Enable Require external ID and paste the external ID from Iru.Attach Organizations read permissions
Attach
AWSOrganizationsReadOnlyAccess, or attach this inline policy:Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
AccessDenied everywhere
AccessDenied everywhere
Confirm role creation happened in the management account.
AssumeRole denied
AssumeRole denied
External ID mismatch.
Considerations
Org APIs evolve: wildcard **Describe* / List***…
Org APIs evolve - wildcard
Describe* / List* pairs reduce churn when AWS ships new read operations.See also
- See Sources Management for the full connector list.