Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About GitHub
The GitHub connector reads repository metadata, branch protection, team membership, organization settings, audit logs, and related security configuration from your GitHub organization. That data appears in Iru Compliance as artifacts you can map to actions and controls. The integration is read-only. Iru does not open pull requests, change settings, or modify repositories beyond what the GitHub API allows for the scopes you grant.How it works
Iru calls the GitHub REST API using a personal access token (PAT) sent as a Bearer token:| Detail | Value |
|---|---|
| Category | Developer tools / source control |
| Authentication | Bearer token (fine-grained or classic PAT) |
| GitHub plan | Compatible with GitHub Free, Team, or Enterprise (subject to GitHub’s own API and audit-log availability) |
Prerequisites
- GitHub access as a member (or owner) of the organization you want Iru to read.
- Owner access on that organization if you need audit logs and org-wide security settings (depending on what your compliance program expects).
- A PAT with read permissions aligned to the tables below (fine-grained PAT shown).
| Area | Permissions |
|---|---|
| Repository | Contents (read), Metadata (read), Administration (read) |
| Organization | Members (read), Administration (read) |
Connect GitHub to Iru
Create a fine-grained personal access token
Open Developer settings
Sign in to GitHub. Select your profile picture → Settings → Developer settings → Personal access tokens → Fine-grained tokens.
Set name, expiration, and resource scope
Set a clear name (for example Iru Compliance) and an expiration (fine-grained PATs can run up to 366 days - set a reminder to rotate early). Under Resource owner, choose your organization when you need organization-level data. Under Repository access, choose All repositories or only what compliance covers.
Set repository and organization permissions
Under Permissions, enable at least the repository and organization read permissions listed under Prerequisites above.
Complete the connector in Iru
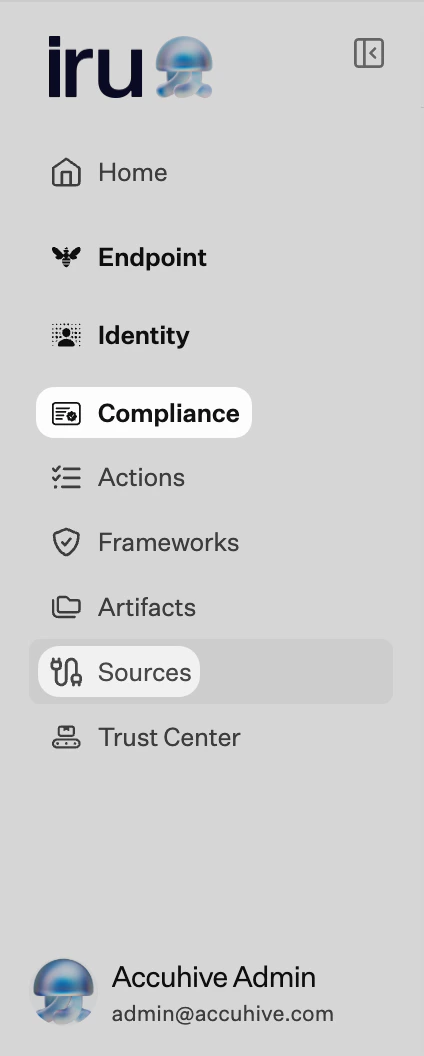
Turn on GitHub
Find GitHub (use Category or Search by name or description). On that card, turn on the toggle. A new tab opens the connector wizard.
Paste the personal access token
When you see the bearer token step, paste your PAT into the Token field and submit.
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
401 Unauthorized
401 Unauthorized
Missing organization data
Missing organization data
For org-wide reads, the PAT’s resource owner must be the organization - not only your personal account. Create a new PAT if needed.
SSO required
SSO required
Authorize the PAT for SAML SSO (see Create a fine-grained personal access token).
Resource not accessible by PAT
Resource not accessible by PAT
Regenerate the PAT with the repository and organization permissions your controls require.
Rate limiting
Rate limiting
Authenticated REST requests share GitHub’s rate limits (see GitHub’s docs). Iru batches work within those limits; sustained spikes can delay sync.
Considerations
Prefer fine-grained PATs with the smallest…
Prefer fine-grained PATs with the smallest repository set and read scopes that still satisfy your controls.
Rotate PATs before expiry and update the connector…
Rotate PATs before expiry and update the connector so evidence collection does not stall.
Iru reads metadata and configuration exposed by the…
Iru reads metadata and configuration exposed by the APIs you allow - it does not bypass GitHub permissions your org enforces.
See also
- See Sources Management for the full connector list.