Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Figma
Iru uses OAuth 2.0 (authorization code). When you enable the source, a browser popup sends you to Figma to sign in and approve scopes (files, projects, org, teams, components, webhooks, analytics, etc.). Some scopes (for examplevariables:read) require Enterprise - lower tiers simply omit those datasets rather than failing outright.
How it works
| Detail | Value |
|---|---|
| Category | Design systems |
| Authentication | OAuth 2.0 |
| Recommended plan | Organization or Enterprise for broad API coverage |
files:read, projects:read, org:read, org_teams:read, components:read, webhooks:write (for incremental updates), and analytics:read - exact lists follow the Figma authorization screen.
Official references: Authentication, Scopes, REST API.
Prerequisites
- Admin or Owner on the Figma organization you want Iru to read.
Connect Figma to Iru
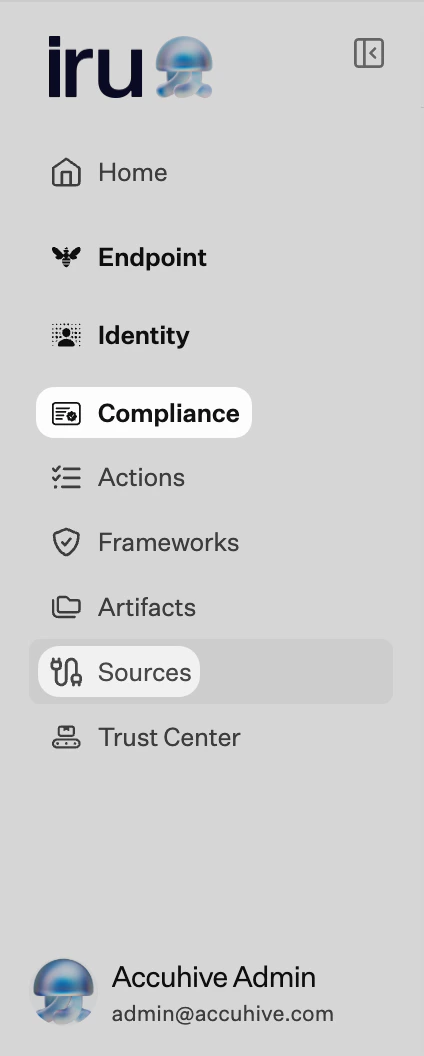
Iru Compliance
Turn on Figma
Find Figma (use Category or Search by name or description). On that card, turn on the toggle. A browser tab or window may open for the connector wizard.
Allow popups and start OAuth
Allow popups for your Iru site if the browser blocks them. Start the OAuth flow from the connector wizard.
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
Popup blocked
Popup blocked
Allow popups for Iru; toggle source off/on.
Access denied
Access denied
Authorize with Org Admin/Owner; Editors may lack org scopes.
Missing teams/files
Missing teams/files
Re-authorize with a user who can access those teams/projects.
Token expired
Token expired
Re-run the OAuth flow from Iru.
Considerations
Removing the authorizing user from the org can…
Removing the authorizing user from the org can invalidate access - reconnect with a durable admin account.
See also
- See Sources Management for the full connector list.