Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Amazon Elastic Compute Cloud (EC2)
The Amazon EC2 connector collects instance inventory, security groups, VPC topology, AMI metadata, and related compute details from your AWS account so you can attach them to controls in Iru Compliance. Iru calls AWS APIs usingsts:AssumeRole into an IAM role you create in your account. The role trusts Iru’s AWS principal and enforces an external ID that the connector wizard shows you. Access is read-only, so Iru does not start, stop, or terminate instances through this source.
How it works
Iru runs in Iru’s AWS account. You create a customer-managed IAM role in your account that:- Trusts Iru’s role ARN (shown in the wizard) only when
sts:ExternalIdmatches the value Iru displays. - Allows read-only EC2 and supporting calls, typically via
AmazonEC2ReadOnlyAccess, or a tighter inline policy if your security team prefers least privilege.
| Detail | Value |
|---|---|
| Category | Cloud compute |
| Authentication | Cross-account IAM role (sts:AssumeRole + external ID) |
Prerequisites
- IAM rights to create roles and attach policies (for example
IAMFullAccessor a narrower admin role). - The Iru principal ARN and external ID from your tenant’s connector screen (not the sample values in examples below unless they match what Iru shows you today).
Connect Amazon EC2 to Iru
Open Iru and copy the trust policy
Turn on AWS Elastic Compute Cloud (EC2)
Find AWS Elastic Compute Cloud (EC2) (use Category or Search by name or description). On that card, turn on the toggle. Keep the wizard tab open for the next steps.
Create the IAM role in AWS
Start the Create role workflow
Sign in to the AWS account that owns your EC2 workload. Open IAM → Roles → Create role.
Configure trusted entity
Choose AWS account → Another AWS account. Enter Iru’s AWS account ID (
753695775620 unless the wizard shows a different value). Enable Require external ID and paste the external ID from the Iru wizard.Attach EC2 read permissions
On Permissions, attach
AmazonEC2ReadOnlyAccess.If your security team does not use the managed policy, attach an inline policy with the JSON below instead:Name the role and copy its ARN
Finish the wizard and name the role (for example
IruEC2ReadOnly). Open the new role and copy the Role ARN from the top of the summary page.Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
AccessDenied on AssumeRole
AccessDenied on AssumeRole
Verify the external ID and principal on the trust policy match Iru’s wizard character-for-character.
Empty inventory
Empty inventory
Confirm the role lives in the same account as your instances and that instances exist in Regions you expect.
Missing security group / VPC data
Missing security group / VPC data
Ensure
ec2:Describe* coverage (managed policy already includes these). Custom policies need matching Describe* actions.Considerations
EC2 APIs are Regional: first sync may take longer…
EC2 APIs are Regional, so first sync may take longer across many Regions.
AmazonEC2ReadOnlyAccess also covers related ELB and…
AmazonEC2ReadOnlyAccess also covers related ELB and Auto Scaling reads for a fuller picture.This integration never mutates instances: it only…
This integration never mutates instances; it only describes them.
See also
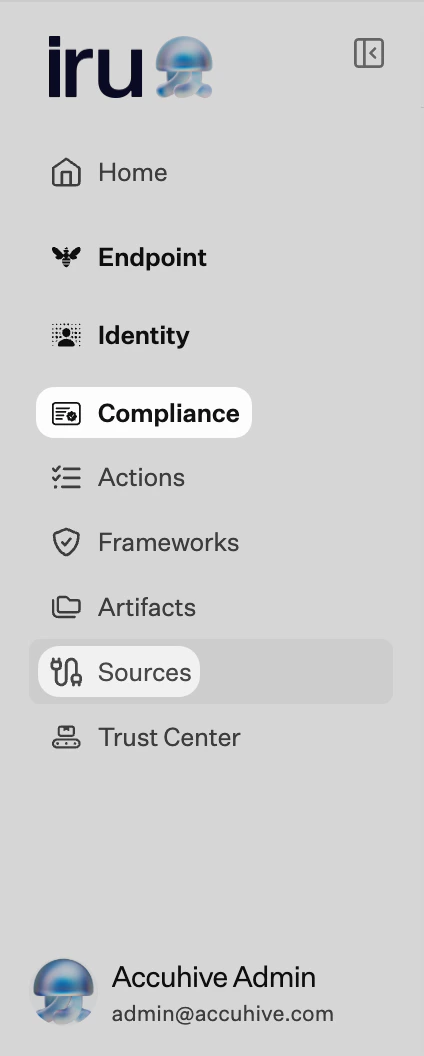
- See Sources Management for the full connector list.