Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Amazon Elastic Kubernetes Service (EKS)
The Amazon EKS connector gathers cluster, node group, add-on, and access entry metadata exposed through the EKS AWS API (distinct from Kubernetes RBAC inside the data plane). Authentication issts:AssumeRole into a customer role with eks:Describe* / eks:List* coverage.
How it works
There is no single AWS-managed “EKS read-only everything” policy for every API surface - start from the inline JSON below unless your platform team publishes a curated variant.| Detail | Value |
|---|---|
| Category | Kubernetes control plane |
| Authentication | Cross-account IAM role |
Prerequisites
- IAM rights to manage roles.
- At least one EKS cluster if you expect immediate inventory.
Connect AWS EKS to Iru
Copy the trust policy from Iru
Turn on AWS EKS
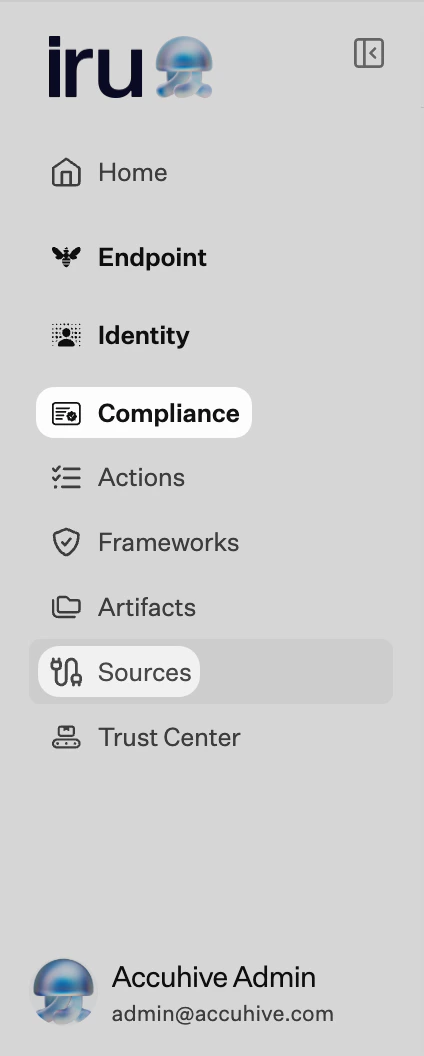
Find AWS EKS (use Category or Search by name or description). On that card, turn on the toggle. Leave the wizard tab open.
Create the IAM role in AWS
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 (or the ID Iru shows). Enable Require external ID and paste the external ID from Iru.Name the role and copy the ARN
Name the role (for example
IruEKSReadOnly), create it, and copy the Role ARN.Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
AssumeRole denied
AssumeRole denied
External ID mismatch.
Partial cluster coverage
Partial cluster coverage
New EKS APIs appear frequently - wildcards keep policies forward-compatible; tighten only with testing.
Considerations
This covers AWS-side EKS APIs: pod-level evidence…
This covers AWS-side EKS APIs - pod-level evidence still belongs to Kubernetes auditing/logging pipelines.
See also
- See Sources Management for the full connector list.