Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Amazon Elastic Container Service (ECS)
The Amazon ECS connector collects clusters, services, tasks, task definitions, and container instance metadata for compliance evidence. AWS does not ship a single-purpose ECS read-only managed policy for this pattern. Use theecs:Describe* / ecs:List* inline JSON below unless your cloud team supplies an equivalent.
How it works
Standardsts:AssumeRole trust toward Iru plus inline permissions covering ECS control-plane reads.
| Detail | Value |
|---|---|
| Category | Containers |
| Authentication | Cross-account IAM role |
Prerequisites
- IAM rights to create roles and inline policies.
- At least one ECS cluster if you expect immediate non-empty results.
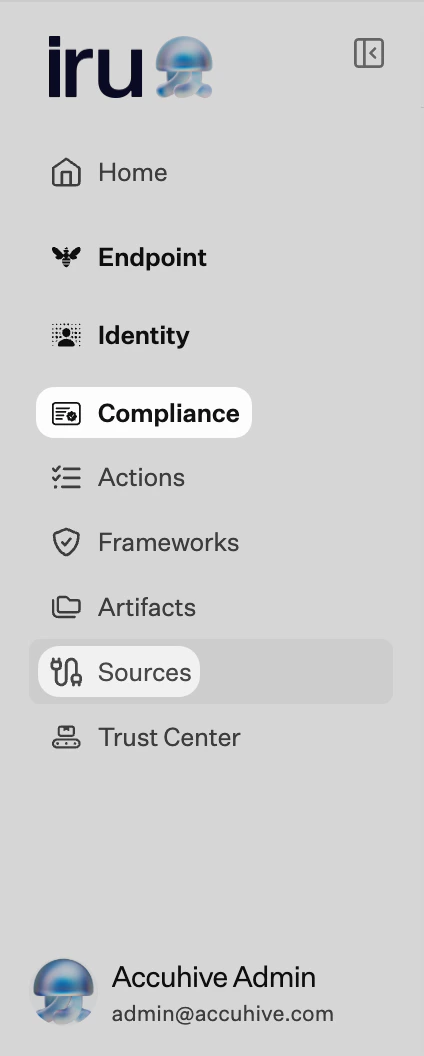
Connect AWS ECS to Iru
Copy the trust policy from Iru
Turn on AWS ECS
Find AWS ECS (use Category or Search by name or description). On that card, turn on the toggle. Leave the wizard tab open.
Create the IAM role in AWS
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 (or the ID Iru shows). Enable Require external ID and paste the external ID from Iru.Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
AssumeRole denied
AssumeRole denied
External ID mismatch.
Missing services
Missing services
Confirm clusters exist in scanned Regions and the inline policy is actually attached.
Considerations
Covers ECS APIs, not workload logs inside…
Covers ECS APIs, not workload logs inside tasks - pair with logging sources if audits require runtime proof.
See also
- See Sources Management for the full connector list.