Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About AWS Lambda
The AWS Lambda connector collects function configuration, layers, event source mappings, concurrency settings, and related metadata across Regions without invoking functions or downloading deployment packages. Iru usessts:AssumeRole into a role you create, gated by an external ID from the wizard.
How it works
Create an IAM role that trusts Iru’s principal and attachAWSLambda_ReadOnlyAccess, or use the tighter inline policy below if your security team prefers least privilege.
| Detail | Value |
|---|---|
| Category | Compute / serverless |
| Authentication | Cross-account IAM role |
Prerequisites
- IAM permission to create roles and attach policies.
- Principal and external ID values copied from your live connector (samples like account
753695775620may differ per tenant).
Connect AWS Lambda to Iru
Copy the trust policy from Iru
Turn on AWS Lambda
Find AWS Lambda (use Category or Search by name or description). On that card, turn on the toggle. Keep the wizard tab open.
Create the IAM role in AWS
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 unless the wizard differs. Enable Require external ID and paste the external ID from Iru.Attach Lambda read permissions
Attach The managed policy covers actions such as
AWSLambda_ReadOnlyAccess, or attach this inline policy:GetFunction, ListFunctions, GetFunctionConfiguration, layers, aliases, and mappings; the inline variant relies on Get* / List* wildcards.Name the role and copy the ARN
Name the role (for example
IruLambdaReadOnly), create it, and copy its ARN.Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
AssumeRole denied
AssumeRole denied
External ID or principal mismatch - re-copy from Iru.
Empty Regional lists
Empty Regional lists
Confirm functions exist in enabled Regions and the role targets the right account.
Encrypted env vars opaque
Encrypted env vars opaque
Read-only APIs may not expose ciphertext details - metadata still evidences configuration presence.
Considerations
Lambda is Regional; first scans walk every enabled…
Lambda is Regional; first scans walk every enabled Region.
Iru does not invoke functions or extract ZIP…
Iru does not invoke functions or extract ZIP artifacts - configuration evidence only.
See also
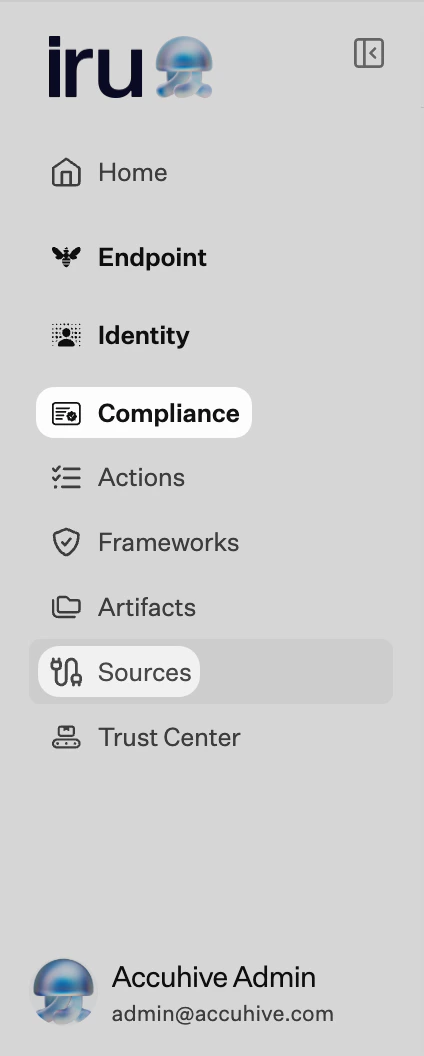
- See Sources Management for the full connector list.