Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About GitLab
The GitLab connector reads project metadata, group membership, branch protection, CI/CD configuration, and (where your plan and token allow) audit-oriented events from your GitLab.com group or self-managed instance. Data appears as artifacts in Iru Compliance for mapping to actions and controls. Iru sends credentials using GitLab’sPRIVATE-TOKEN header - typically with a personal access token so reads can span the groups and projects you choose.
How it works
GitLab’s REST API authenticates with thePRIVATE-TOKEN header:
| Detail | Value |
|---|---|
| Category | Developer tools / source control |
| Authentication | PRIVATE-TOKEN header (personal access token recommended) |
| Hosting | GitLab SaaS or self-managed |
Prerequisites
- GitLab access to the groups and projects compliance cares about.
- Group Owner or Maintainer where you need membership and audit-style reads (exact needs depend on your controls).
- For self-managed GitLab, confirm Iru targets your instance base URL (not only
gitlab.com).
| Scope | Purpose |
|---|---|
read_api | Broad read access to API endpoints used for inventory and configuration evidence |
read_repository | Repository metadata aligned to branch protection and repo settings |
read_user | User profile reads needed for membership evidence |
Connect GitLab to Iru
GitLab
Open personal access tokens
Sign in to GitLab. Select your avatar → Edit profile → Access Tokens, then Add new token.
Set token name, expiration, and scopes
Enter a name (for example Iru Compliance). Set an expiration (GitLab requires one; maximum duration may be limited by your administrator). Choose the scopes from Prerequisites.
Iru Compliance
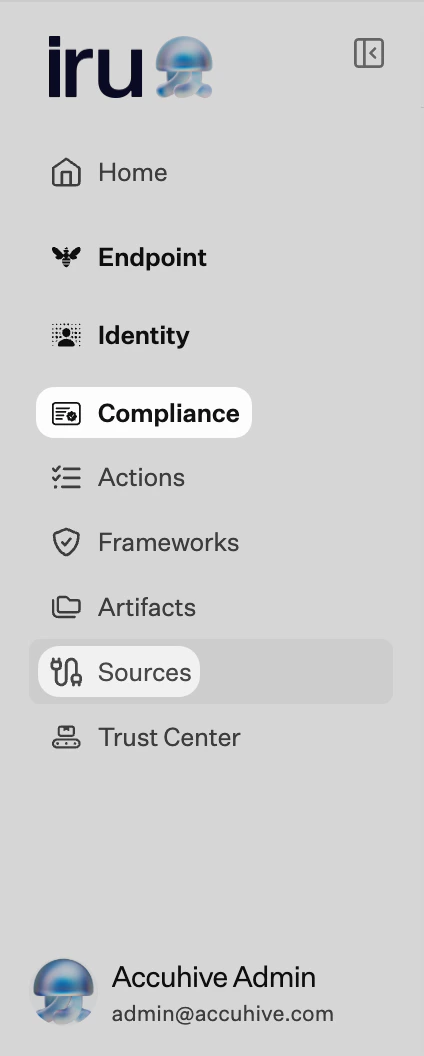
Turn on GitLab
Find GitLab (use Category or Search by name or description). On that card, turn on the toggle. A browser tab or window may open for the connector wizard.
Paste the personal access token
When the wizard asks for the
PRIVATE-TOKEN value, paste your token and submit.Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
401 Unauthorized
401 Unauthorized
403 Forbidden
403 Forbidden
Increase scopes or elevate project/group role - your token cannot read endpoints your account cannot access.
Self-managed URL issues
Self-managed URL issues
Ensure the integration points at your instance hostname and that network paths allow Iru’s outbound calls.
Missing audit-class events
Missing audit-class events
Some audit APIs require Premium/Ultimate features - compare your GitLab tier to the evidence your framework expects.
Considerations
Tokens expire on a schedule: rotate early and update…
Tokens expire on a schedule - rotate early and update the connector.
GitLab applies rate limits; large groups may take…
GitLab applies rate limits; large groups may take longer during first sync.
Iru reads configuration exposed by the API: it does…
Iru reads configuration exposed by the API - it does not rewrite pipelines or repository settings.
See also
- See Sources Management for the full connector list.