Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About AWS Key Management Service (KMS)
The AWS Key Management Service connector gathers key metadata, aliases, policies, grants, tags, and rotation status so controls can prove how keys are governed. Iru usessts:AssumeRole with an external ID. The recommended inline policy below avoids kms:Decrypt and other cryptographic data operations (metadata only).
How it works
SkipAWSKeyManagementServicePowerUser for this use case - it bundles write-style capabilities. Use the explicit inline JSON from the wizard path or the template below.
| Detail | Value |
|---|---|
| Category | Security / cryptography |
| Authentication | Cross-account IAM role |
Prerequisites
- IAM admin rights to publish roles.
- Live connector strings (principal, external ID).
Connect AWS KMS to Iru
Copy the trust policy from Iru
Turn on AWS KMS
Find AWS KMS (use Category or Search by name or description). On that card, turn on the toggle. Leave the wizard tab open.
Create the IAM role in AWS
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 (unless your wizard lists another ID). Enable Require external ID and paste the external ID from Iru.Skip broad managed policies
Advance without attaching
AWSKeyManagementServicePowerUser or other broad KMS write-capable policies.Attach the metadata-only inline policy
Add this inline policy:
No
kms:Decrypt, kms:Encrypt, or GenerateDataKey. Iru cannot use your keys to process ciphertext.Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
AssumeRole denied
AssumeRole denied
Fix external ID drift.
Sparse CMK details
Sparse CMK details
Resource policies on individual keys may deny
DescribeKey - adjust key policies if auditors require full visibility.AWS-managed keys
AWS-managed keys
Always listed but sometimes less introspectable than customer-managed keys - expected per AWS behavior.
Considerations
Keys are Regional: inventory spans enabled Regions.
Keys are Regional; inventory spans enabled Regions.
Works purely off API metadata: no key material…
Works purely off API metadata - no key material leaves KMS through decrypt calls from this connector.
See also
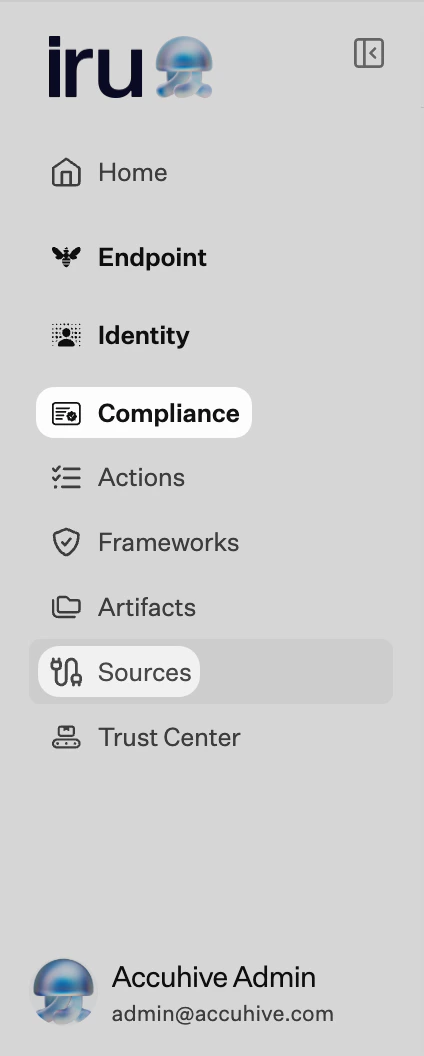
- See Sources Management for the full connector list.