Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About AWS IAM Identity Center (Identity Store)
This source reads users, groups, and memberships through theidentitystore: API - the directory layer behind IAM Identity Center. Permission sets, account assignments, and SSO applications live under sso: and are covered by IAM Identity Center (SSO). Create the role in your organization management or delegated administrator account where Identity Center is enabled.
AWS does not ship a minimal managed policy only for Identity Store. Use the inline JSON below.
How it works
| Detail | Value |
|---|---|
| Category | Identity |
| Authentication | Cross-account IAM role |
Prerequisites
- IAM Identity Center enabled; role in management or delegated admin account.
d-xxxxxxxxxxIdentity Store ID is discoverable in console Settings once Iru connects.
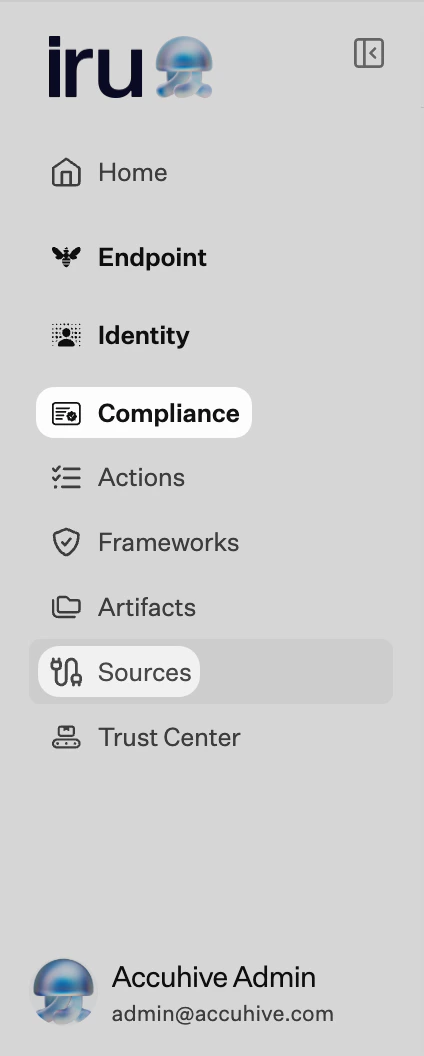
Connect Identity Store to Iru
Copy the trust policy from Iru
Turn on AWS IAM Identity Center (Identity Store)
Find AWS IAM Identity Center (Identity Store) (use Category or Search by name or description). On that card, turn on the toggle. Leave the wizard tab open.
Create the IAM role in AWS
Start Create role
In the management or delegated administrator account, open IAM → Roles → Create role.
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 (or the ID Iru shows). Enable Require external ID and paste the external ID from Iru.Skip broad managed policies
Advance without attaching
AWSSSOReadOnly unless your team standardized on it - Identity Store reads are narrower.Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
Empty directory
Empty directory
Wrong account - use management or delegated admin where Identity Center runs.
AccessDenied on actions
AccessDenied on actions
Use
identitystore:, not sso:.AssumeRole denied
AssumeRole denied
External ID mismatch.
Considerations
Identity Center home Region is fixed per…
Identity Center home Region is fixed per organization; evidence reflects that deployment model.
See also
- AWS IAM Identity Center (SSO)
- See Sources Management for the full connector list.