Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About HashiCorp Vault
Iru reads secrets engine mounts, auth method configuration, named policies, audit devices, and related sys/ metadata using the Vault HTTP API. Each request sends your client token inX-Vault-Token. Iru collects configuration evidence - not secret plaintext values.
Works with Vault OSS, Enterprise (namespaces may need extra setup), and HCP Vault.
How it works
vault_addr (for example https://vault.example.com:8200), then accepts the token.
| Detail | Value |
|---|---|
| Category | Secrets management |
| Authentication | Client token (X-Vault-Token) |
Prerequisites
- A Vault cluster reachable from Iru (network / firewall / PrivateLink as applicable).
- Permission to create a policy and token (or AppRole) with read-only
sys/access as in the example below.
Example read-only policy (HCL)
Save as a.hcl file and apply with vault policy write iru-compliance your-file.hcl.
Connect HashiCorp Vault to Iru
Apply the policy and issue a token
Write the policy file
Save the example policy from above as an
.hcl file on a machine that can reach Vault (for example iru-compliance.hcl).Create a renewable token
Create a renewable token bound to that policy (for example
vault token create -policy=iru-compliance -ttl=720h -renewable=true. Copy the hvs. token value.Complete the connector in Iru
Turn on HashiCorp Vault
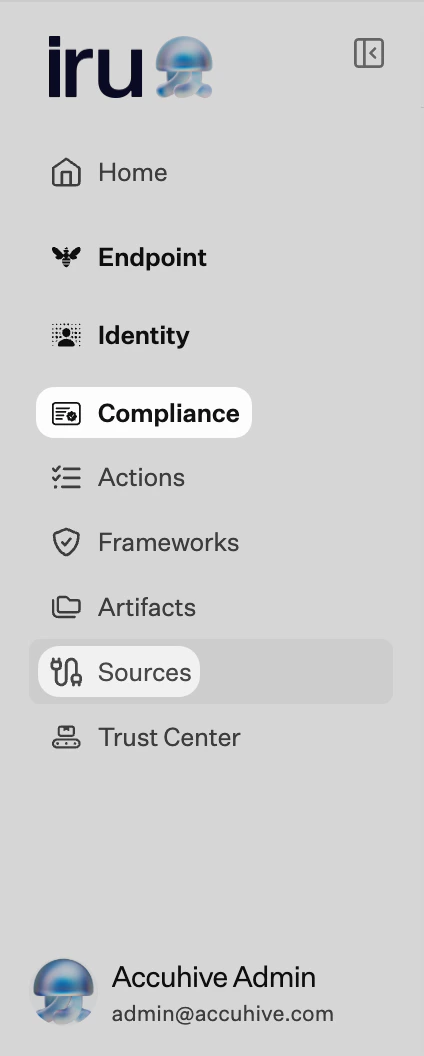
Find HashiCorp Vault (use Category or Search by name or description). On that card, turn on the toggle. A browser tab or window may open for the connector wizard.
Configure server variables
Enter
vault_addr (for example https://vault.example.com:8200) and confirm server variables when prompted.Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
Server variables failed
Server variables failed
Refresh the wizard by toggling the source; re-enter
vault_addr.403 permission denied
403 permission denied
Attach
iru-compliance policy to the token; check Enterprise namespaces.Token expired
Token expired
Issue a new token and update Iru; enable renewal or use AppRole rotation.
Connection refused
Connection refused
Hostname, port (8200), TLS, and outbound routes from Iru.
503 sealed
503 sealed
Unseal Vault before testing.
Considerations
Vault Enterprise namespaces may require paths or…
Vault Enterprise namespaces may require paths or settings beyond this baseline - coordinate with your Vault admins.
See also
- See Sources Management for the full connector list.