Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About AWS CloudTrail
CloudTrail evidence typically includes management events viaLookupEvents plus configuration metadata for trails. LookupEvents covers roughly the last 90 days - older analytics require S3 archive permissions (s3:GetObject) and possibly kms:Decrypt when trails use customer-managed CMKs.
How it works
AttachAWSCloudTrail_ReadOnlyAccess. Add the optional inline kms:Decrypt statement only when you deliberately ingest encrypted trail archives from S3.
| Detail | Value |
|---|---|
| Category | Audit logging |
| Authentication | Cross-account IAM role |
Prerequisites
- IAM rights to create roles.
- Awareness whether audits demand API lookups only vs S3 archive depth.
Connect AWS CloudTrail to Iru
Copy the trust policy from Iru
Turn on AWS CloudTrail
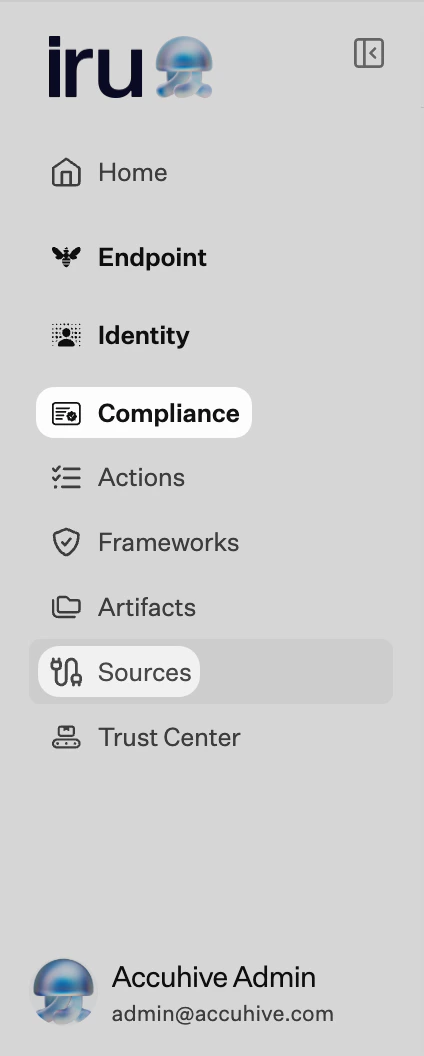
Find AWS CloudTrail (use Category or Search by name or description). On that card, turn on the toggle. Leave the wizard tab open.
Create the IAM role in AWS
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 (or the ID Iru shows). Enable Require external ID and paste the external ID from Iru.Optional - add KMS decrypt for encrypted trail archives
If your trail archives use a customer-managed KMS key, add an inline policy (replace REGION, ACCOUNT, CMK-ID):
Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
Events older than ~90 days missing
Events older than ~90 days missing
Use S3 archive ingestion paths - requires
s3:GetObject + optional kms:Decrypt.AssumeRole denied
AssumeRole denied
External ID mismatch.
Considerations
Multi-Region / Organization trails affect where…
Multi-Region / Organization trails affect where APIs must run - mirror AWS best practices for centralized logging.
See also
- See Sources Management for the full connector list.