Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Okta
The Okta connector reads directory data, group memberships, application assignments, policies, MFA posture, and audit-related signals from your Okta org and surfaces them as artifacts in Iru Compliance. Authentication uses an Okta API token over the Okta Management API. The integration is intended for read-only evidence collection. Iru does not provision users or change policies in Okta beyond what your token’s admin permissions allow during API reads.How it works
Okta accepts API tokens using the SSWS scheme:| Detail | Value |
|---|---|
| Category | Security / identity |
| Authentication | Okta API token (Authorization: SSWS YOUR_TOKEN) |
| Okta plan | Any plan that includes Management API access you rely on |
Prerequisites
- An Okta administrator role that can create API tokens (Super Admin, Org Admin, or Read-only Admin, depending on what your org allows for automation accounts).
- Your org’s subdomain or full Okta domain (for example
acmeif users sign in athttps://acme.okta.com).
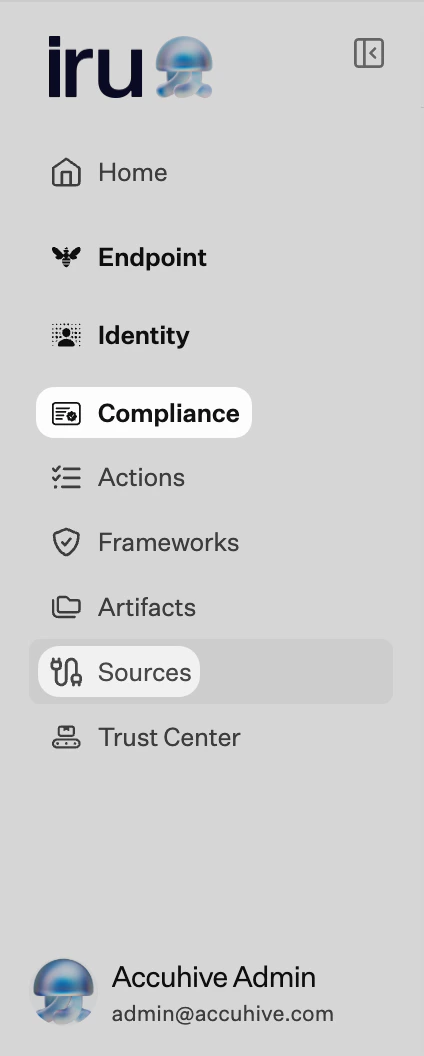
Connect Okta to Iru
Okta
Create an API token in Okta
Sign in to the Okta Admin Console. Go to Security → API → Tokens. Select Create token, enter a name you will recognize (for example Iru Compliance), then create and copy the token immediately. You cannot view it again after you leave the dialog.Plan for idle expiry: if no successful API call uses the token for 30 days, Okta invalidates it and you must create a new token.Optionally restrict token use by network zone if your environment uses fixed egress IPs.
Iru Compliance
Turn on Okta
Find Okta (use Category or Search by name or description). On that card, turn on the toggle. A new tab opens the connector wizard.
Choose the server URL that matches your tenant
Select the row that matches where your org lives:
Confirm your choice so the wizard can build the correct Management API base URL.
| Environment | Base URL pattern |
|---|---|
| Production (US) | https://YOUR_SUBDOMAIN.okta.com |
| EMEA | https://YOUR_SUBDOMAIN.okta-emea.com |
| Preview / sandbox | https://YOUR_SUBDOMAIN.oktapreview.com |
| US Gov | https://YOUR_SUBDOMAIN.okta-gov.com |
| Custom domain | https://YOUR_OKTA_DOMAIN |
Enter subdomain and domain variables
Follow each wizard screen: enter your subdomain or domain values where prompted so OAuth-related URLs stay consistent with your tenant.
Mid-wizard steps that mention OAuth URLs exist because the connector template configures endpoints completely. SSWS token authentication on the last step is what Iru uses for Management API reads for this source.
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
401 Unauthorized
401 Unauthorized
Token expired
Token expired
Recreate the token under Security → API → Tokens if it has been idle for 30 days.
403 Forbidden
403 Forbidden
The admin profile tied to the token may lack read access to some endpoints. Confirm at least Read-only Admin (or equivalent) for evidence you need.
Wrong host / domain
Wrong host / domain
Disconnect and reconnect, double-checking subdomain and region (US vs EMEA vs Gov vs preview).
Considerations
Treat API tokens like credentials
Treat API tokens like credentials. Prefer a service account with the minimum admin role that still satisfies evidence requirements.
Okta applies rate limits to Management API traffic;…
Okta applies rate limits to Management API traffic; large orgs may see longer sync times during first collection.
Iru reads data exposed by the APIs your token can…
Iru reads data exposed by the APIs your token can access - it cannot override Okta entitlements you do not grant.
See also
- See Sources Management for the full connector list.