Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Microsoft Azure Storage
The Microsoft Azure Storage source reads storage account settings, blob container metadata, container access policies, lifecycle management rules, and network rules through Azure Resource Manager. Iru does not read blob contents, file share data, queue messages, or table rows; it collects only configuration and container-level metadata the management API returns. Authentication is delegated OAuth 2.0 (Microsoft Entra ID) as the user who completes the wizard. Iru does not modify storage accounts, containers, or policies. For a full subscription inventory, assign Reader at subscription scope. Reader scoped only to a resource group can hide accounts in other groups.How it works
Iru uses Microsoft’s OAuth 2.0 authorization code flow against Azure Resource Manager. The requested scope is:https://management.azure.com/user_impersonation
| Detail | Value |
|---|---|
| Category | Developer tools |
| Authentication | OAuth 2.0 (Microsoft Entra ID, Azure Resource Manager) |
| Vendor plan | Any Azure subscription with storage resources |
What Iru collects
| Data type | Notes |
|---|---|
| Storage accounts | Name, location, SKU (LRS, GRS, ZRS), kind, access tier, TLS version, network rules |
| Blob containers | Container names, public access settings, metadata |
| Container access policies | Stored access policies and their permissions |
| Lifecycle management policies | Tier transitions and deletion rules |
| Network rules | Firewall rules, service endpoints, private endpoints |
Microsoft.Storage/*/read for account and container metadata through ARM, not data-plane access to object contents.
Official references: Azure Storage documentation, Storage Resource Provider REST API, Storage built-in roles, Authorize access with Azure RBAC.
Prerequisites
- Microsoft Entra ID sign-in to the Azure portal.
- Reader (or higher) on the subscription you connect. Assign at subscription scope for complete visibility.
- Browser pop-ups allowed so the connector wizard can open when you enable the source.
Connect Microsoft Azure Storage to Iru
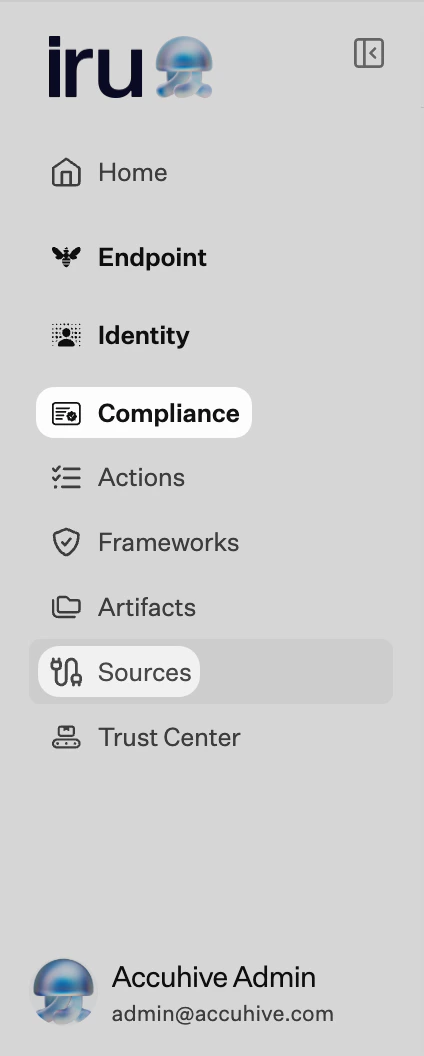
Connection is configured in Iru Compliance. The wizard shows Step 1 of 1: Perform OAuth Authentication.Iru Compliance
Turn on the integration
Find Microsoft Azure Storage (set Category to Developer tools or use Search by name or description). On that card, turn on the toggle to start the connector wizard.
Launch OAuth and sign in
Select Launch OAuth Authentication. Sign in with an account that has Reader on the subscription. Accept the requested permissions.
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
Storage accounts not listed
Storage accounts not listed
Confirm Reader at subscription scope if you expect accounts across the whole subscription. Reader scoped only to a resource group omits accounts elsewhere.
Wrong Microsoft Entra tenant
Wrong Microsoft Entra tenant
Sign out of the Microsoft pop-up and sign in with the account for the correct tenant.
Broken status
Broken status
Turn Microsoft Azure Storage off and on in Sources, then complete OAuth again.
See also
- See Sources Management for the full connector list.