Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Microsoft Azure Authorization
The Microsoft Azure Authorization source reads Azure RBAC role assignments and role definitions, plus Azure Policy definitions and assignments, from the subscription you connect. Evidence in Iru reflects who can access what and which policies are assigned; Iru does not write changes back to Azure. Iru uses delegated OAuth 2.0 against Azure Resource Manager on behalf of the user who signs in, so collections respect that user’s existing Azure permissions.How it works
Iru uses Microsoft’s OAuth 2.0 authorization code flow (delegated permissions) against Azure Resource Manager (management.azure.com). After you sign in and consent in the pop-up, Iru receives a short-lived access token and renews it automatically (including rotating refresh tokens where applicable).
The OAuth scope requested is:
https://management.azure.com/user_impersonation
That grants read access to ARM APIs as the signed-in user, limited by that user’s RBAC on the subscription.
| Detail | Value |
|---|---|
| Category | Developer tools |
| Authentication | OAuth 2.0 (Microsoft Entra ID, Azure Resource Manager) |
| Vendor plan | Any Azure subscription |
What Iru collects
| Data type | Azure ARM resource type |
|---|---|
| Role assignments | Microsoft.Authorization/roleAssignments |
| Role definitions (built-in and custom) | Microsoft.Authorization/roleDefinitions |
| Azure Policy definitions | Microsoft.Authorization/policyDefinitions |
| Azure Policy assignments | Microsoft.Authorization/policyAssignments |
Prerequisites
- Microsoft Entra ID account that can sign in at the Azure portal.
- At minimum the built-in Reader role (or equivalent read access) on the subscription you want Iru to read. That includes
Microsoft.Authorization/*/readfor assignments, definitions, and policy metadata. - Browser pop-ups allowed so the connector wizard can open when you enable the source.
Connect Microsoft Azure Authorization to Iru
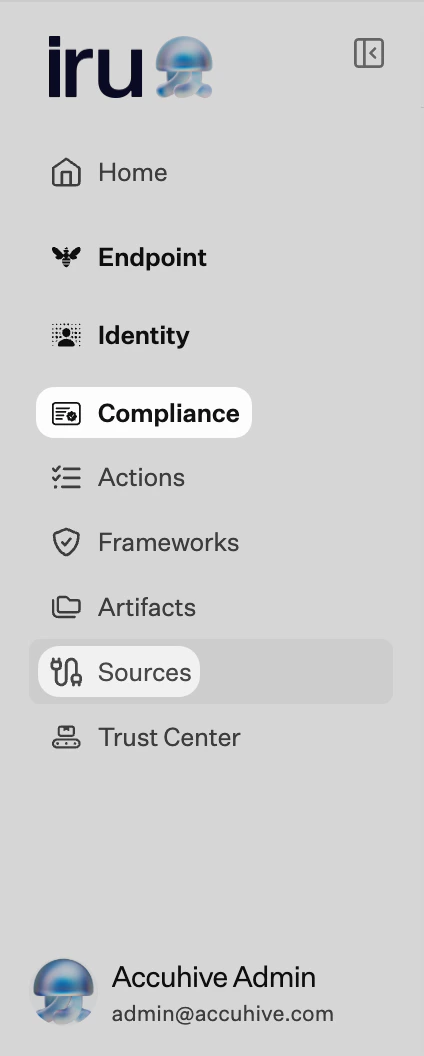
Connection is configured in Iru Compliance (sidebar and connector wizard). The wizard shows Step 1 of 1: Perform OAuth Authentication.Iru Compliance
Turn on the integration
Find Microsoft Azure Authorization (set Category to Developer tools or use Search by name or description). On that card, turn on the toggle to start the connector wizard.
Launch OAuth and sign in
Select Launch OAuth Authentication. Sign in with Microsoft Entra ID using the account that has Reader (or equivalent) on the target subscription. Review permissions and Accept.
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
Insufficient privileges or empty data
Insufficient privileges or empty data
Confirm the authenticating account has the Reader role on the subscription (see Prerequisites).
Wrong Microsoft Entra tenant
Wrong Microsoft Entra tenant
If your organization has several tenants, sign out of the Microsoft pop-up and sign in with the account for the correct tenant.
Broken status or re-authentication
Broken status or re-authentication
Access tokens renew about every hour while the connection is active. If refresh is interrupted (for example after long inactivity), the card may show Broken. Turn the source off and on, then complete OAuth again.
See also
- See Sources Management for the full connector list.