Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Microsoft Azure Network
The Microsoft Azure Network source reads virtual network layout, network security groups, Azure Firewall policy, route tables, load balancers, and public IP configuration from your subscription through Azure Resource Manager. Authentication is delegated OAuth 2.0 (Microsoft Entra ID) as the user who completes the wizard. Iru does not change network resources. For subscription-wide visibility, assign Reader at subscription scope. Roles granted only on individual resource groups can hide resources outside those groups.How it works
Iru uses Microsoft’s OAuth 2.0 authorization code flow against Azure Resource Manager. The requested scope is:https://management.azure.com/user_impersonation
| Detail | Value |
|---|---|
| Category | Developer tools |
| Authentication | OAuth 2.0 (Microsoft Entra ID, Azure Resource Manager) |
| Vendor plan | Any Azure subscription with network resources |
What Iru collects
| Data type | Notes |
|---|---|
| Virtual networks (VNets) | Address spaces, subnets, DNS settings, peering |
| Network security groups (NSGs) | Inbound and outbound rules, associated subnets and NICs |
| Azure Firewalls | Rules, threat intelligence, DNS proxy settings |
| Route tables | User-defined routes and subnet associations |
| Load balancers | Front-end IPs, backend pools, rules, health probes |
| Public IP addresses | Allocation method, DNS labels, associations |
Microsoft.Network/*/read for these resource types (no write permissions).
Official references: Virtual Network documentation, Network security groups, Networking built-in roles, Network REST API.
Prerequisites
- Microsoft Entra ID sign-in to the Azure portal.
- Reader (or higher) on the subscription you connect. Assign at subscription scope for full inventory.
- Browser pop-ups allowed so the connector wizard can open when you enable the source.
Connect Microsoft Azure Network to Iru
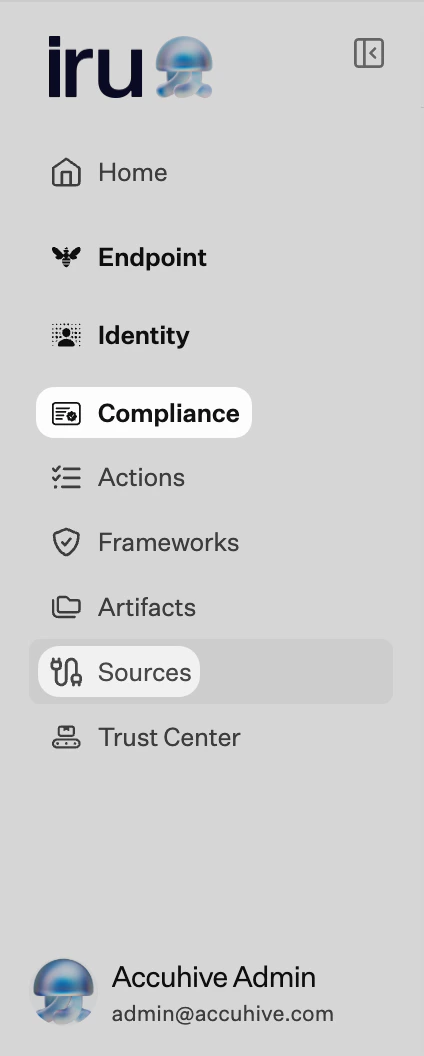
Connection is configured in Iru Compliance. The wizard shows Step 1 of 1: Perform OAuth Authentication.Iru Compliance
Turn on the integration
Find Microsoft Azure Network (set Category to Developer tools or use Search by name or description). On that card, turn on the toggle to start the connector wizard.
Launch OAuth and sign in
Select Launch OAuth Authentication. Sign in with an account that has Reader on the subscription. Accept the requested permissions.
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
Empty or partial network inventory
Empty or partial network inventory
Confirm Reader is assigned at subscription scope if you expect a full subscription view. Reader scoped only to a resource group may omit resources in other groups.
Wrong Microsoft Entra tenant
Wrong Microsoft Entra tenant
Sign out of the Microsoft pop-up and sign in with the account for the correct tenant.
Broken status
Broken status
Turn Microsoft Azure Network off and on in Sources, then complete OAuth again.
See also
- See Sources Management for the full connector list.