Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Amazon DynamoDB
The Amazon DynamoDB connector inventories tables, capacity settings, indexes, and related resources for compliance mapping. Iru assumes an IAM role in your account (sts:AssumeRole + external ID) and does not bulk-export item payloads as evidence - focus stays on configuration and inventory APIs.
How it works
UseAmazonDynamoDBReadOnlyAccess, or the inline policy below if you want explicit actions (includes PartiQLSelect / Query / Scan read paths present in the managed policy set - align with your security review).
| Detail | Value |
|---|---|
| Category | Databases |
| Authentication | Cross-account IAM role |
Prerequisites
- IAM rights to create roles and inline policies.
- Connector principal and external ID from Iru.
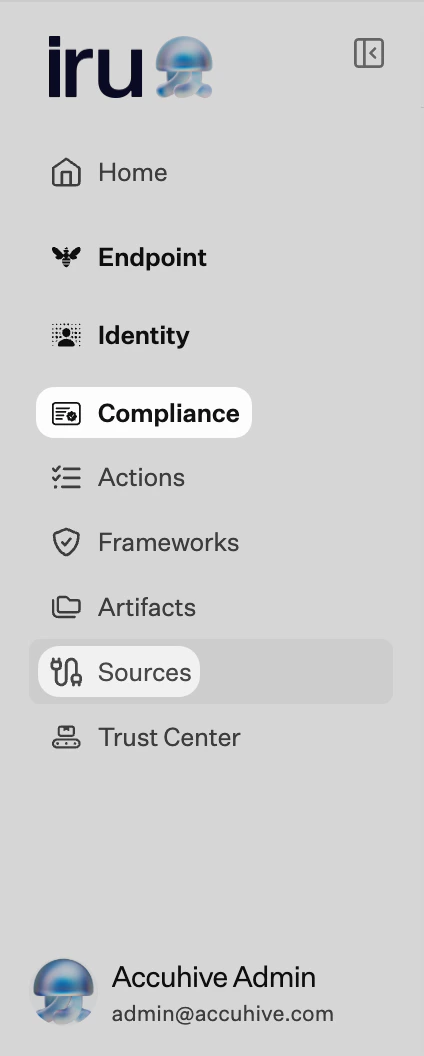
Connect AWS DynamoDB to Iru
Copy the trust policy from Iru
Turn on AWS DynamoDB
Find AWS DynamoDB (use Category or Search by name or description). On that card, turn on the toggle. Leave the wizard tab open.
Create the IAM role in AWS
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 (or the ID Iru shows). Enable Require external ID and paste the external ID from Iru.Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
AssumeRole denied
AssumeRole denied
External ID mismatch.
Regional gaps
Regional gaps
Tables live in specific Regions - ensure the role’s account matches asset ownership.
DAX
DAX
Managed policy includes DAX reads; custom policies may need
dax:Describe* / dax:List*.Considerations
Global tables and related resources may appear per replica Region.
Global tables and related resources may appear per replica Region.
Scope IAM to what audits truly need: narrower…
Scope IAM to what audits truly need - narrower policies reduce accidental data-plane reads.
See also
- See Sources Management for the full connector list.