Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Snowflake
Iru collects warehouse and account usage, database/schema metadata, roles and grants, and login/query history from Snowflake, primarily viaSNOWFLAKE.ACCOUNT_USAGE views. Authentication uses key-pair authentication: short-lived JWTs signed with your RSA private key, verified against the public key registered on the Snowflake user Iru uses.
How it works
| Detail | Value |
|---|---|
| Category | Data platform |
| Authentication | Key-pair JWT |
Prerequisites
SECURITYADMIN(or equivalent) to assignRSA_PUBLIC_KEYon a dedicated service user.- OpenSSL (or another tool) to generate a 2048-bit (or larger) RSA key pair.
- Your account identifier (
orgname-accountnamepreferred, or legacy locator with region/cloud if required).
Connect Snowflake to Iru
Snowflake
Generate an RSA key pair
Example with OpenSSL:Protect
snowflake_private_key.pem. Never commit it or share it with Snowflake.Register the public key on a Snowflake user
As an administrator, strip the PEM headers and newlines from Snowflake allows two keys per user (
snowflake_public_key.pem so only the base64 body remains, then run:RSA_PUBLIC_KEY / RSA_PUBLIC_KEY_2) for rotation. Assign the new key to RSA_PUBLIC_KEY_2, update Iru, then drop the old key.Produce a JWT for the wizard
Use Snowflake CLI or a library. For example:Copy the JWT string for the initial Iru handshake; ongoing regeneration is handled in product.
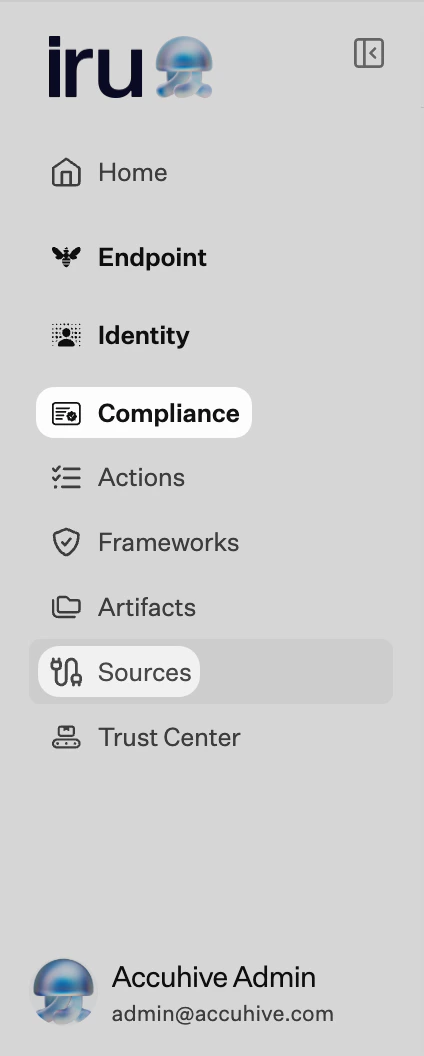
Iru Compliance
Turn on Snowflake
Find Snowflake (use Category or Search by name or description). On that card, turn on the toggle. A browser tab or window may open for the connector wizard.
Enter account and host in the wizard
Choose the host pattern that matches your account:
- Standard:
https://YOUR_ACCOUNT_IDENTIFIER.snowflakecomputing.com - PrivateLink:
https://YOUR_ACCOUNT_IDENTIFIER.privatelink.snowflakecomputing.com
account_identifier and confirm server variables before continuing.Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
Server variables failed
Server variables failed
Wizard session expired. Toggle the source off and on, then retry.
JWT validation / 401
JWT validation / 401
Run
DESCRIBE USER to confirm the fingerprint matches and the private key pairs with the registered public key.Wrong account string
Wrong account string
Prefer
org-account form; legacy locators may need region/cloud suffix.PrivateLink
PrivateLink
Ensure Iru egress can reach your endpoint; allowlist if required.
Missing ACCOUNT_USAGE
Missing ACCOUNT_USAGE
IMPORTED PRIVILEGES on SNOWFLAKE for the Iru role.Considerations
Iru does not run arbitrary queries against your…
Iru does not run arbitrary queries against your tables. It reads governance-oriented metadata and usage views.
See also
- See Sources Management for the full connector list.