Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Amazon Simple Storage Service (S3)
The Amazon S3 connector inventories bucket configuration: policies, encryption, versioning, logging, notifications, public-access blocks, and related settings without reading object payloads. Iru assumes an IAM role you create in your account (sts:AssumeRole with an external ID). This keeps evidence focused on how buckets are configured, not on stored file contents.
How it works
You publish a role whose trust policy references Iru’s AWS principal and mandates the external ID string from the wizard. For permissions, prefer the inline policy below instead ofAmazonS3ReadOnlyAccess alone - the managed policy includes s3:GetObject, which your security team may not want for a metadata-only integration.
| Detail | Value |
|---|---|
| Category | Object storage |
| Authentication | Cross-account IAM role |
Prerequisites
- IAM rights to create roles and attach inline policies.
- The live principal + external ID pair from your connector - not necessarily the sample IDs printed in older screenshots.
Connect Amazon S3 to Iru
Copy the trust policy from Iru
Turn on AWS S3
Find AWS S3 (use Category or Search by name or description). On that card, turn on the toggle. Leave the wizard tab open.
Create the IAM role in AWS
Configure trusted entity
Choose AWS account → Another AWS account. Enter
753695775620 (or the ID Iru shows). Enable Require external ID and paste the value from Iru.Skip broad managed policy (optional)
Advance past the managed policy picker without attaching
AmazonS3ReadOnlyAccess if you plan to use the metadata-only inline policy in the next step.Create the metadata-only inline policy
Create the role with a placeholder name if required, then open the role → Permissions → Create inline policy → JSON editor. Paste:Save the inline policy.
This policy intentionally excludes
s3:GetObject and related object-read APIs so Iru cannot pull object bodies - only bucket-level metadata.Submit the role ARN in Iru
Troubleshooting
Nothing opens when you turn the source on
Nothing opens when you turn the source on
Check pop-up blocker settings for the Iru site and try again.
AssumeRole denied
AssumeRole denied
External ID mismatch - re-copy from Iru without stray spaces.
Missing bucket policy rows
Missing bucket policy rows
Bucket resource policies can deny cross-account reads even when IAM allows them.
Encryption settings absent
Encryption settings absent
Confirm
s3:GetEncryptionConfiguration stayed in the inline policy.Considerations
Buckets are regional, but ListAllMyBuckets is…
Buckets are regional, but
ListAllMyBuckets is global - expect multi-Region follow-up calls during inventory.Explicit Deny statements in bucket policies block…
Explicit Deny statements in bucket policies block reads regardless of IAM allows - document expectations with auditors.
See also
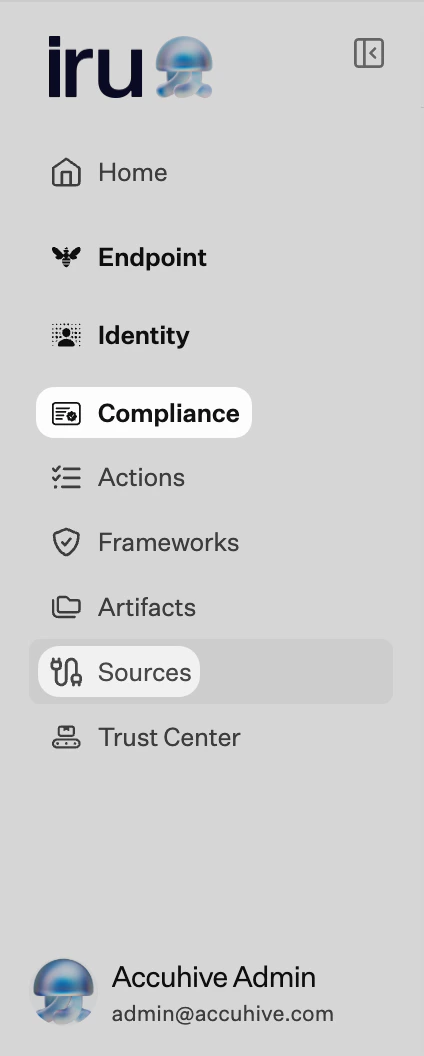
- See Sources Management for the full connector list.