Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
This guide applies to Mac computers
About Passport with Microsoft Entra ID Web Login
Passport with Microsoft Entra ID Web Login signs users in through a web view of your organization’s Microsoft Entra ID sign-in page, so Conditional Access and MFA can run at login. For Mac Login (username and password at the Mac login window without that web view), use Configure Passport with Microsoft Entra ID - Mac Login.How It Works
Passport integrates with your Microsoft Entra ID tenant at the macOS login screen. In Web Login mode, users complete Entra ID sign-in (including MFA when required) in that web view before the local Mac session is created or updated.Prerequisites
You need access to a Microsoft Entra ID admin account to grant the Passport app the correct permissions. For MFA settings in Microsoft Entra ID, see Microsoft’s MFA configuration guide.- Microsoft Entra ID
- Iru Endpoint
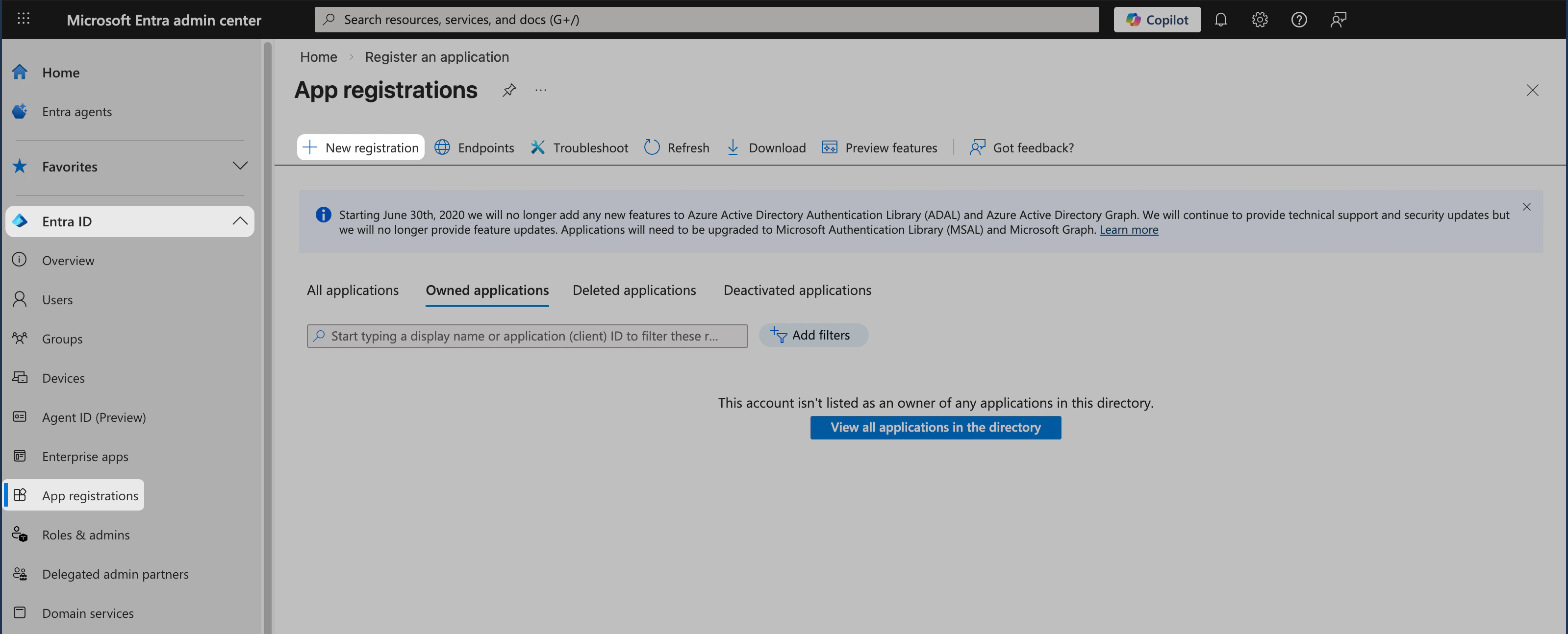
Create the App Registration
Sign in to Microsoft Entra admin center
Sign in to the Microsoft Entra admin center using a Global Administrator account.
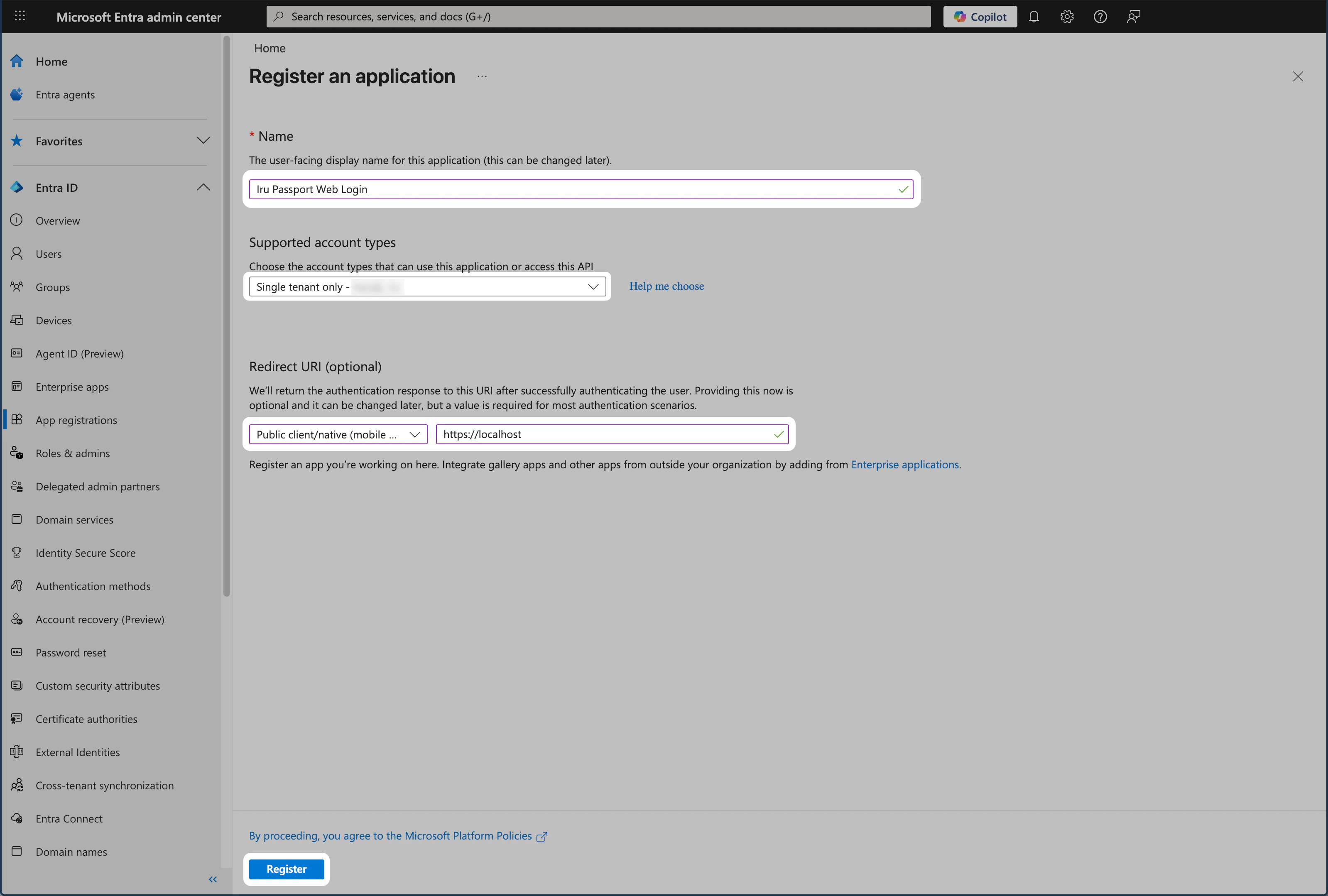
Set Redirect URI platform
In the Redirect URI section, open the Select a platform drop-down and choose Public client/native (mobile & desktop).
Enter redirect URI
In the URI field, enter For more information about redirect URI restrictions, platform types, and best practices, see Microsoft’s redirect URI documentation.
https://localhost. You will use this redirect URI when you configure the Passport Library Item.Collecting Configuration Details
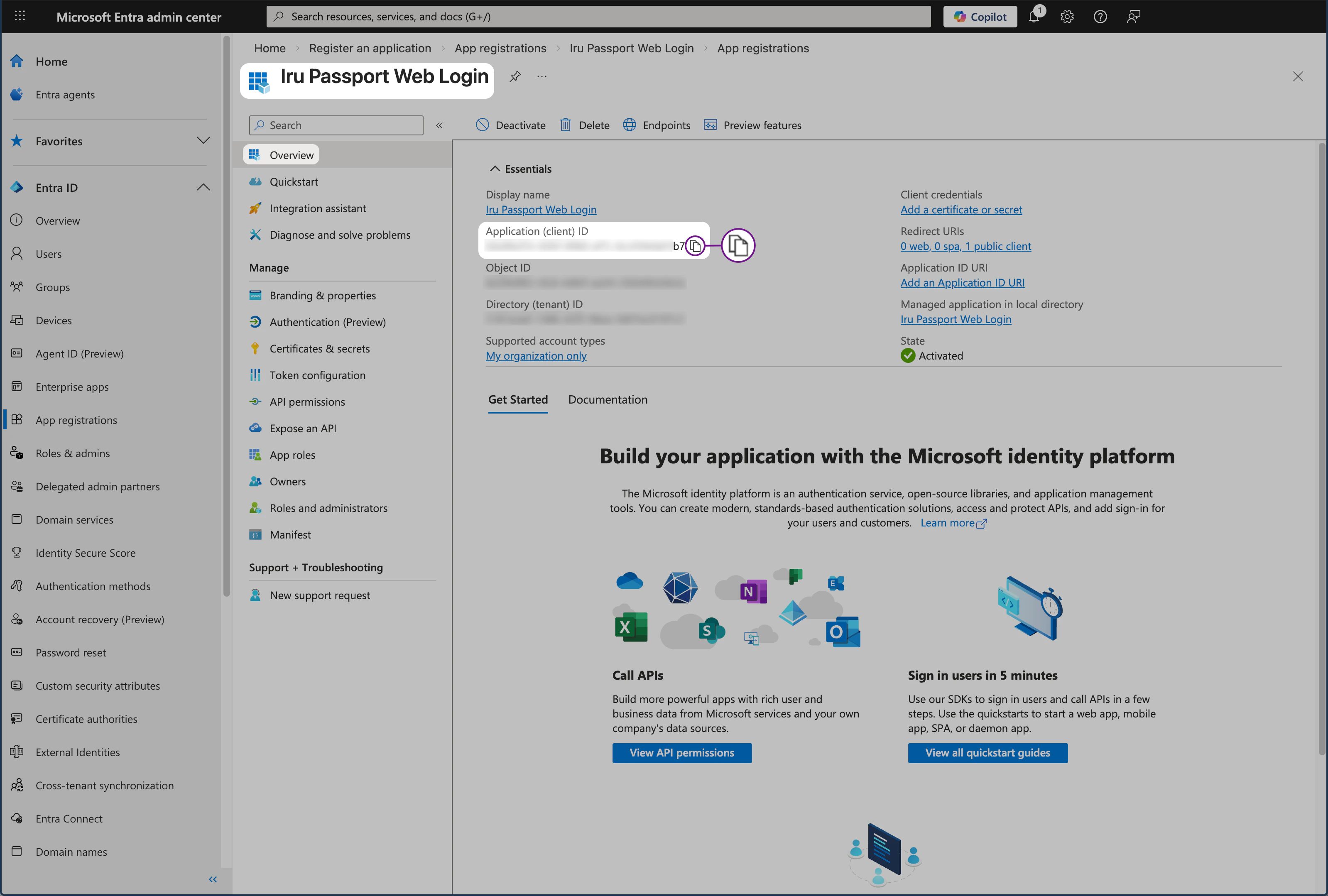
Open a secure text document where the values for this OIDC app can be temporarily stored. You will need these details when you configure the Passport Library Item.Overview Pane
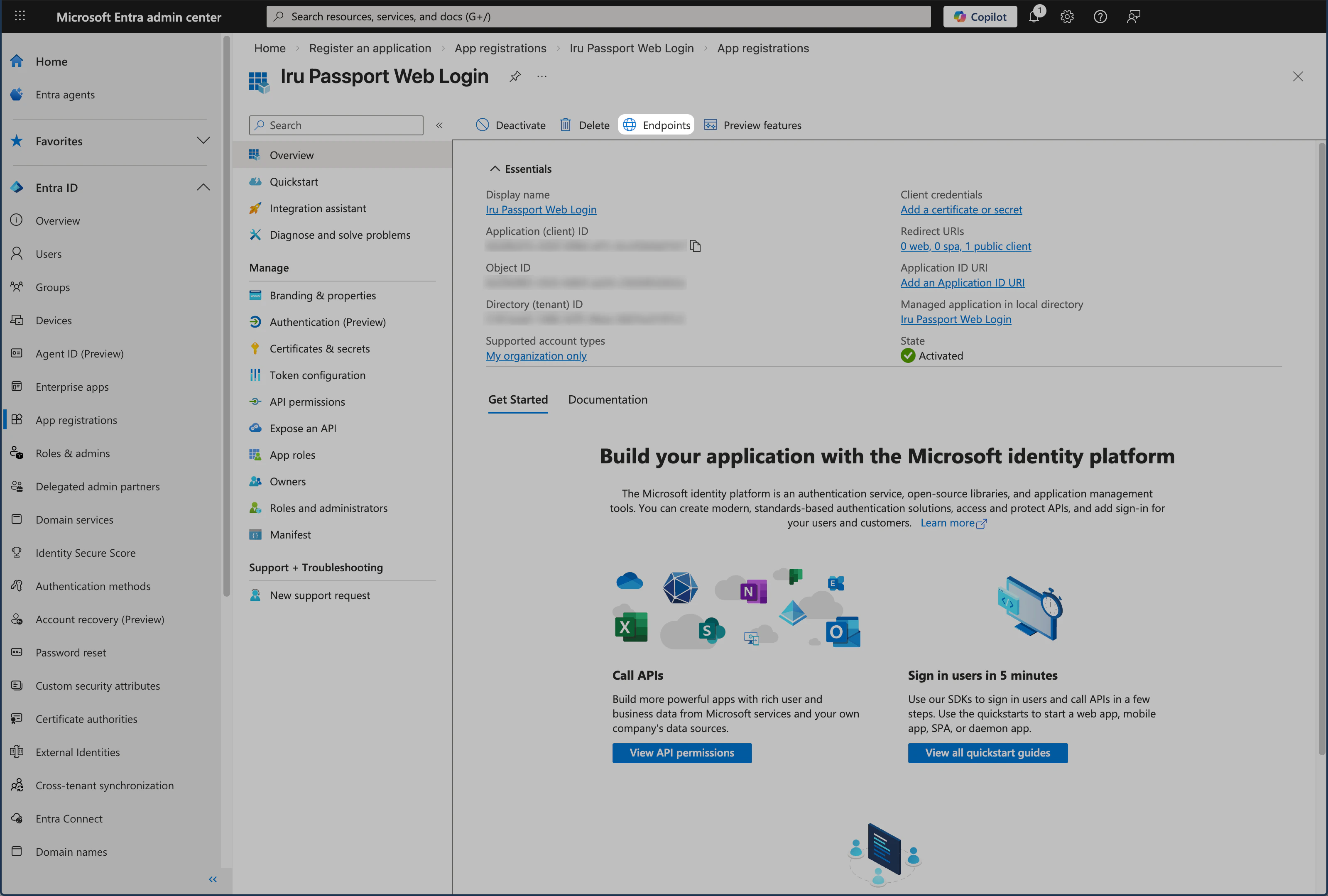
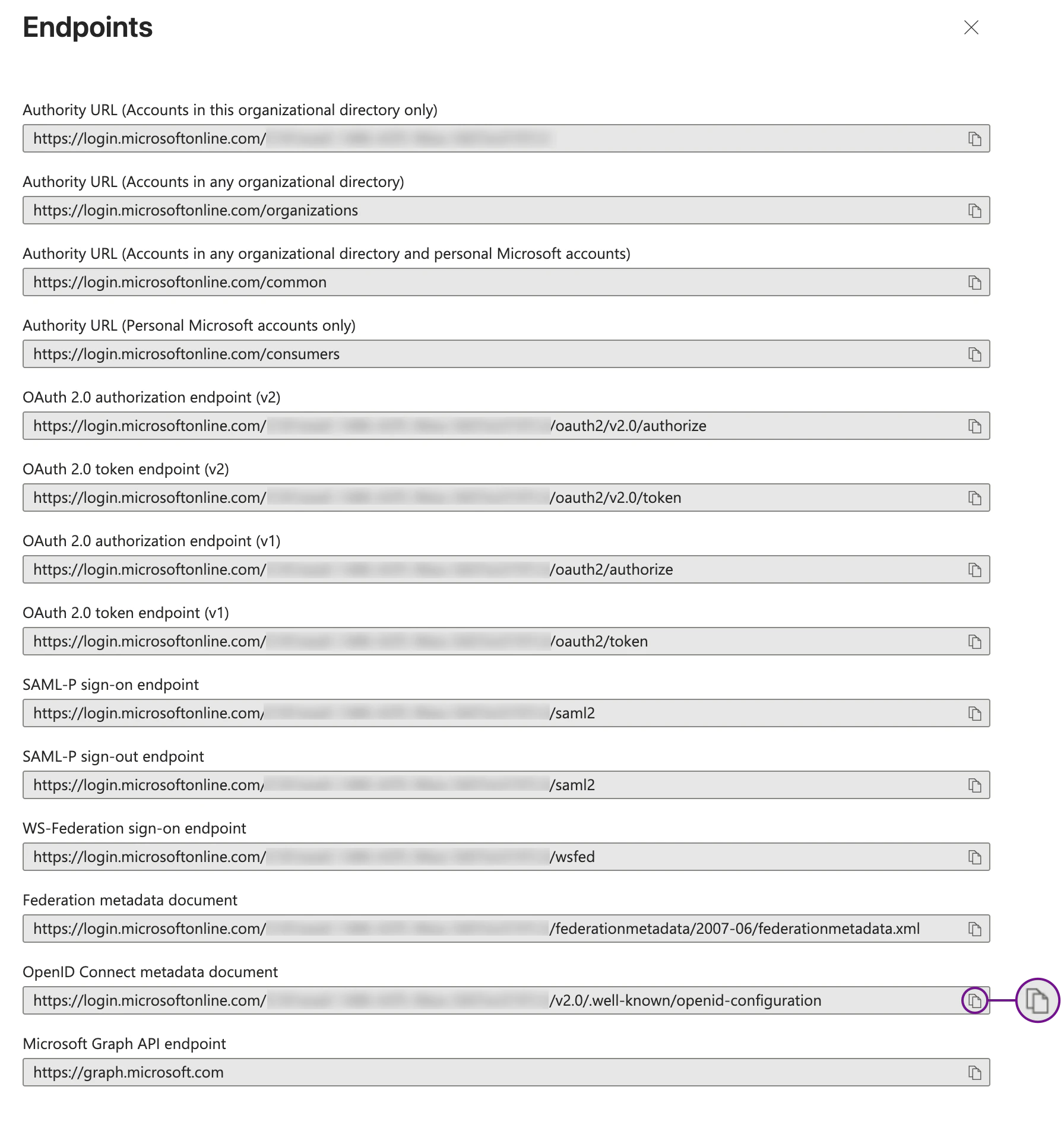
Copy the application (client) ID from the app’s overview. You will need it for the Passport Library Item.Endpoints Pane
Copy the OpenID Connect metadata URL from Endpoints; this is the identity provider URL Passport uses to discover sign-in and token endpoints.Copy Identity provider URL
Copy the OpenID Connect metadata document (identity provider URL) to your secure document.
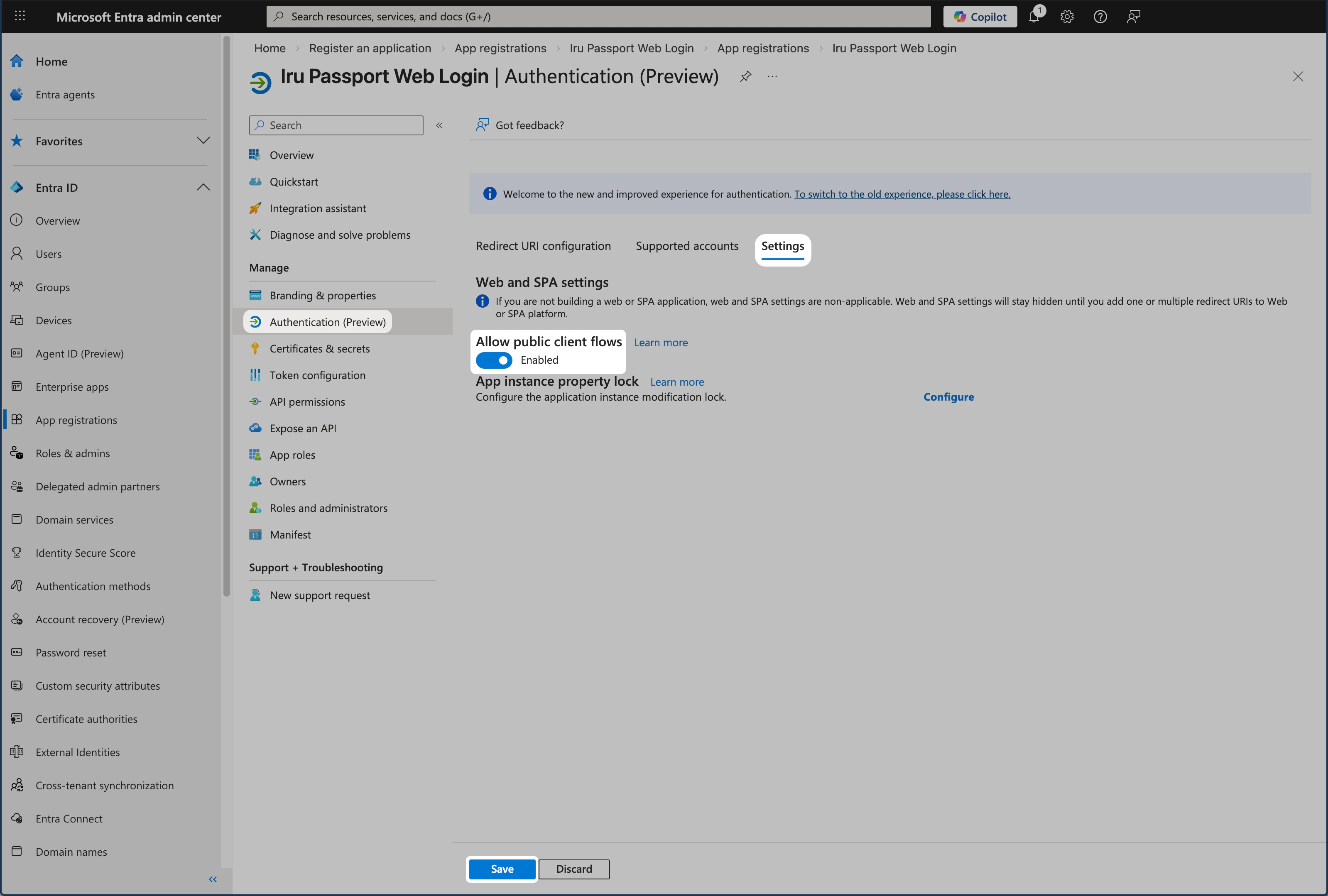
Authentication (Preview) pane
Enable public client flows so the Mac app can complete the sign-in flow without a client secret.Open the Authentication (Preview) pane
In the left menu, select Authentication (Preview) to open that pane.
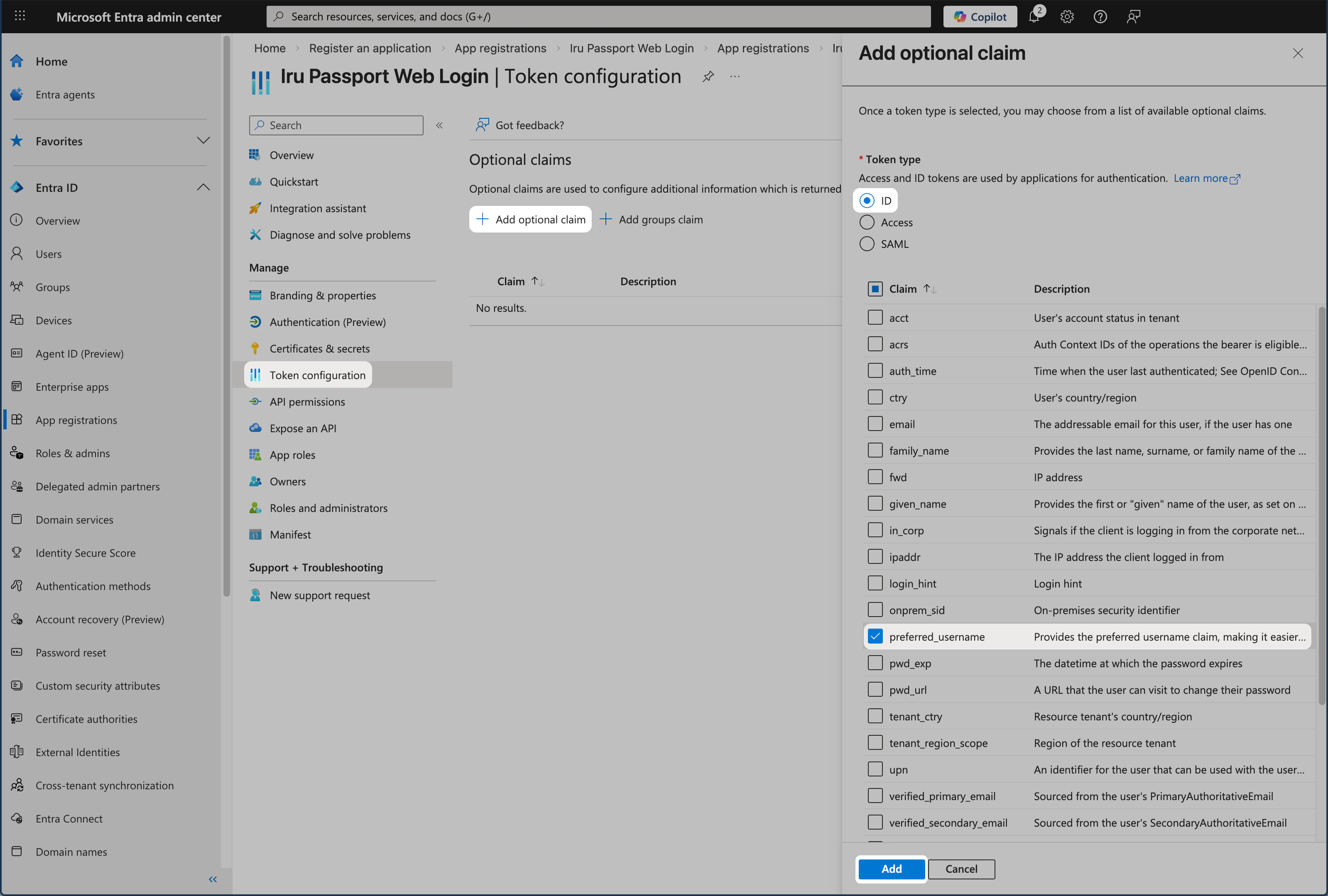
Token Configuration Pane
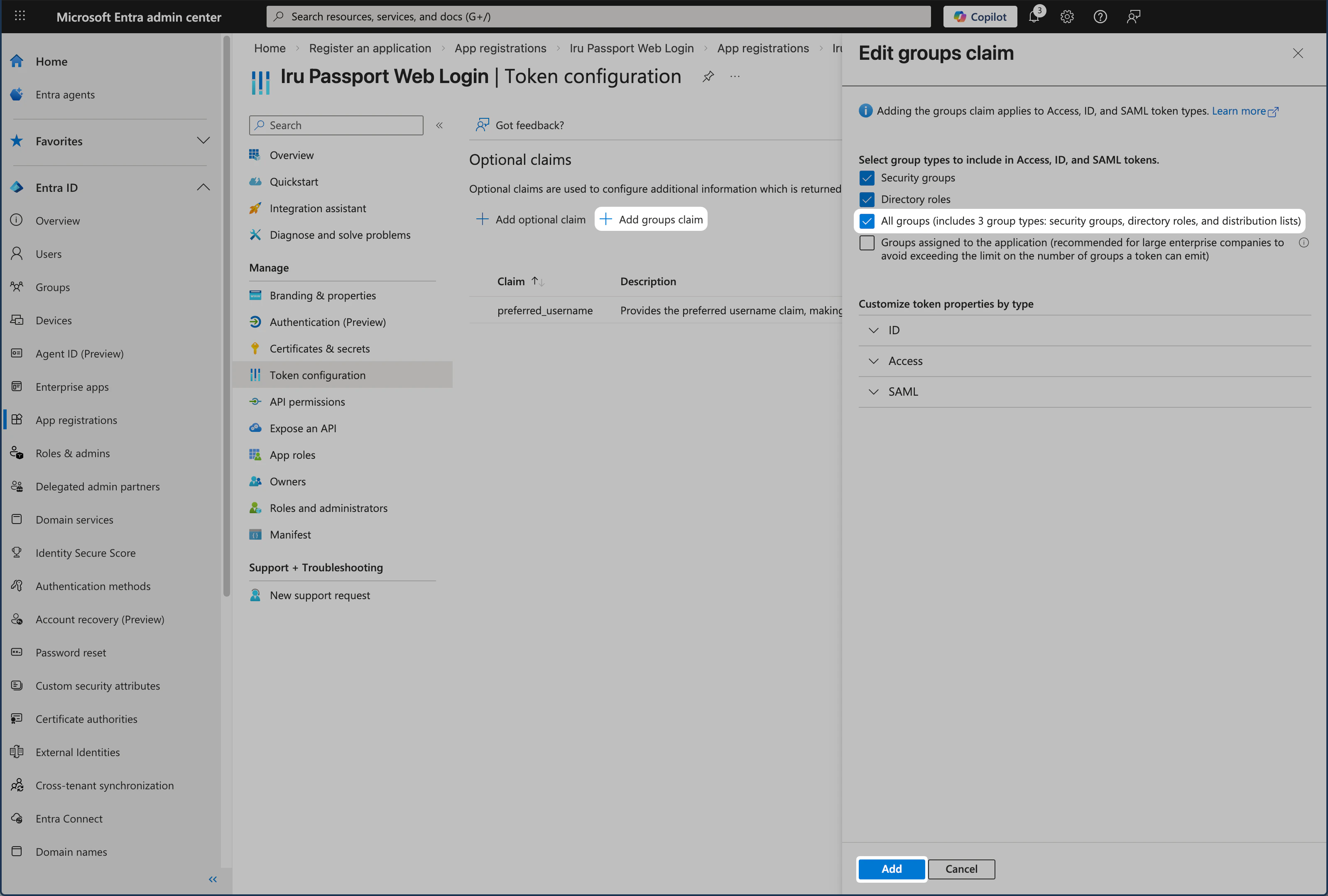
Add the required claims so the token includes the username and group membership Passport needs.Select groups
Select All groups.
Entra ID SAML only supports up to 150 security groups. If you have more than 150 security groups, you should not use All groups, but rather select specific groups. You can read more in Microsoft’s Configure group claims for applications by using Microsoft Entra ID article.
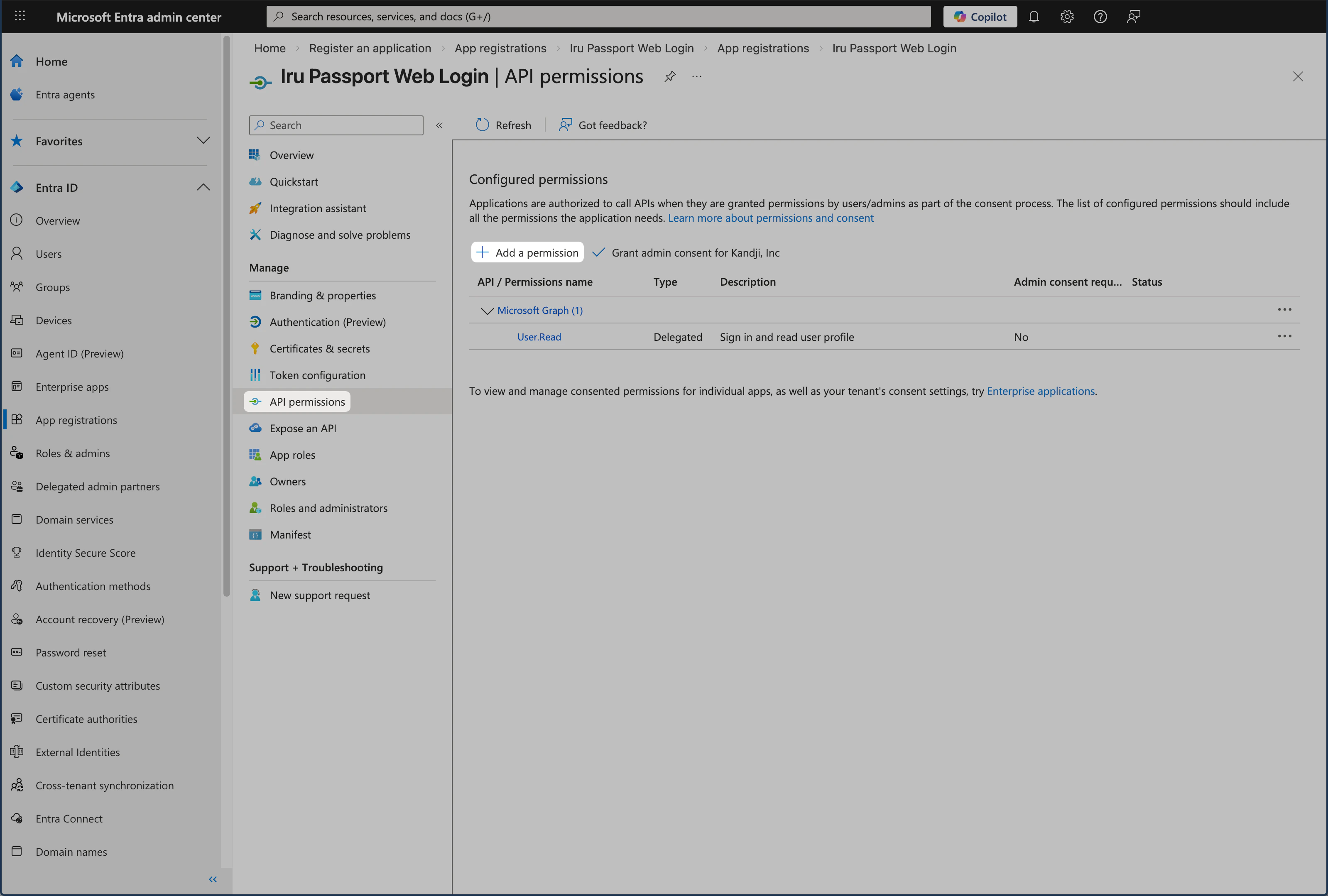
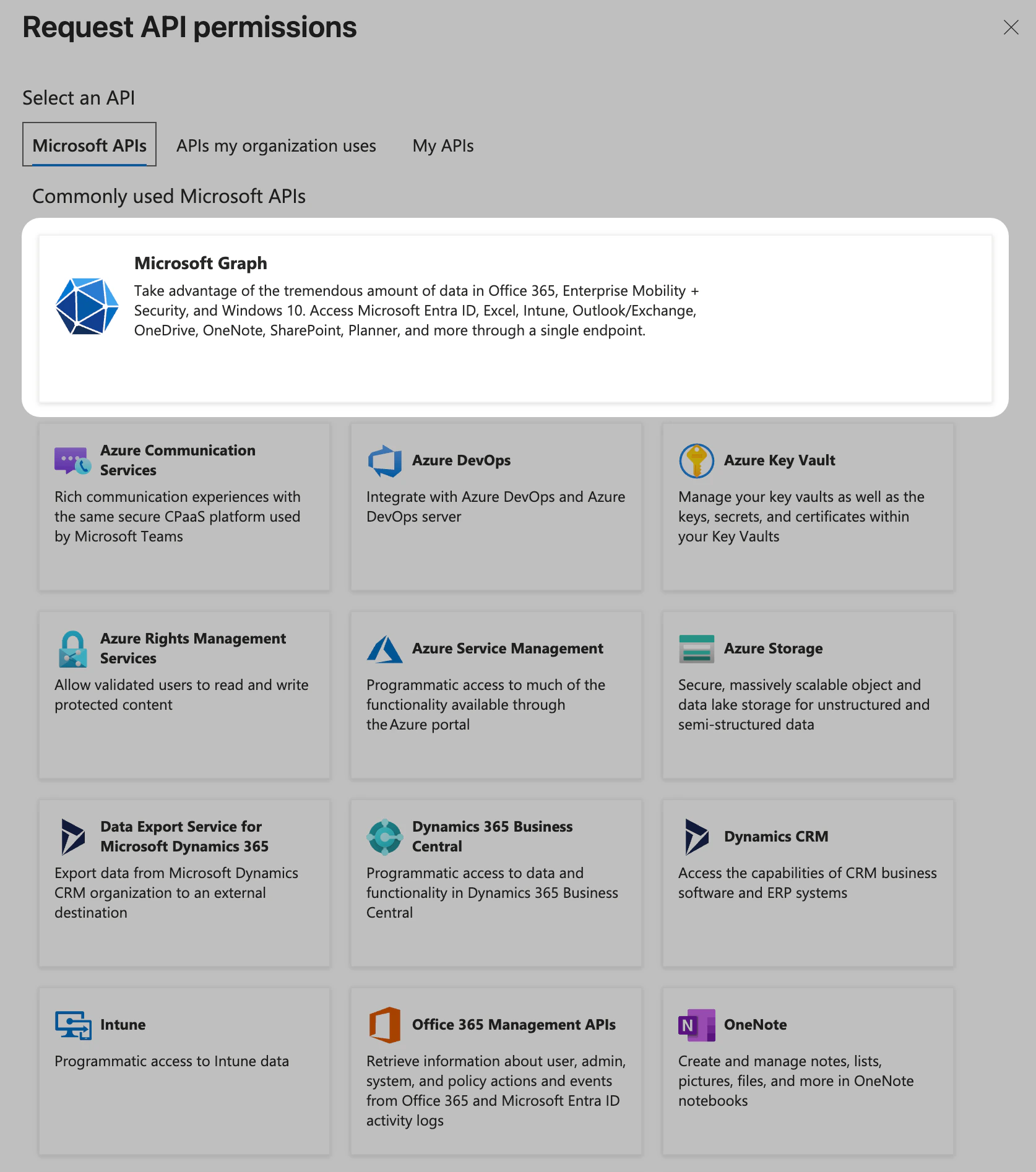
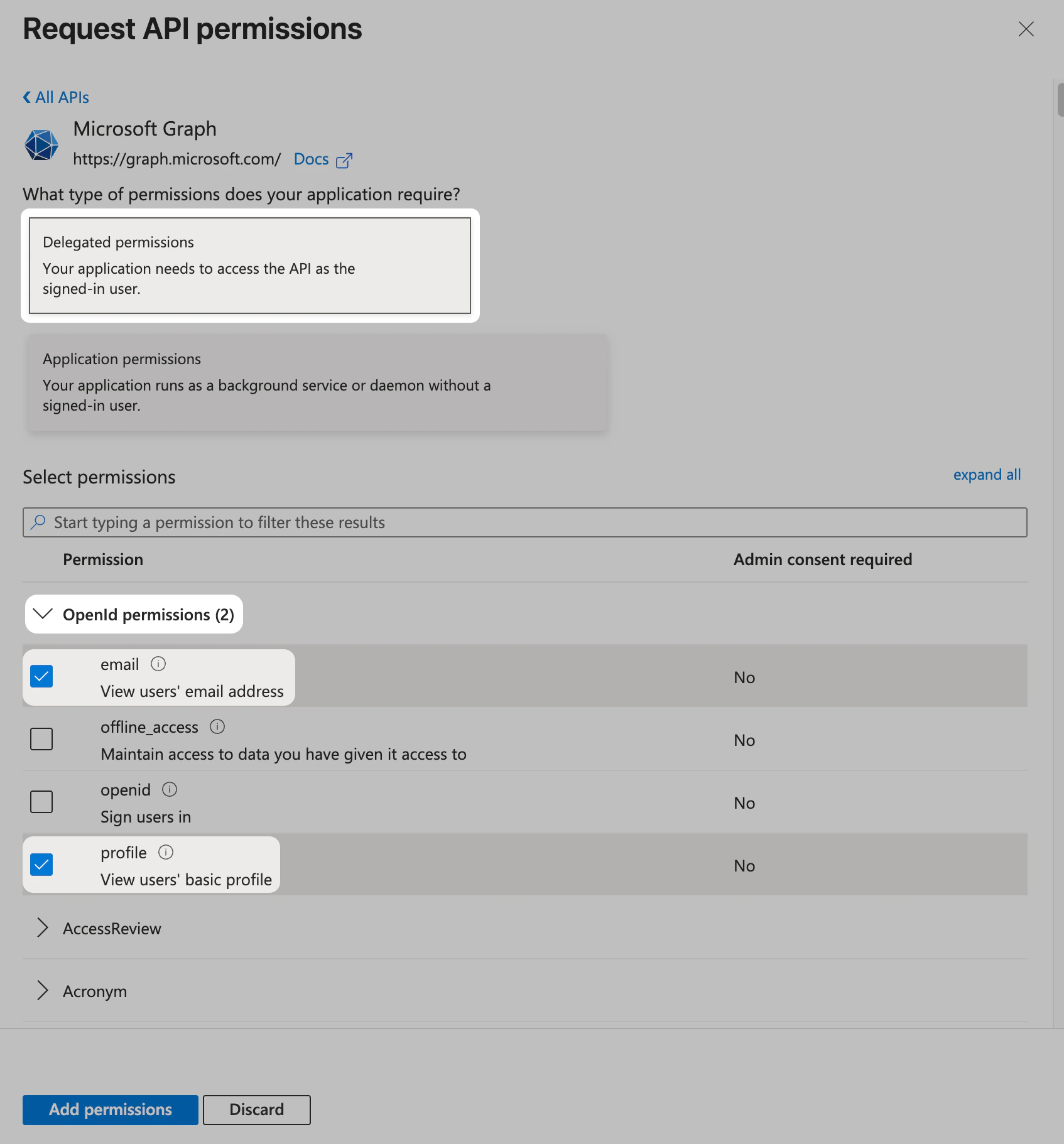
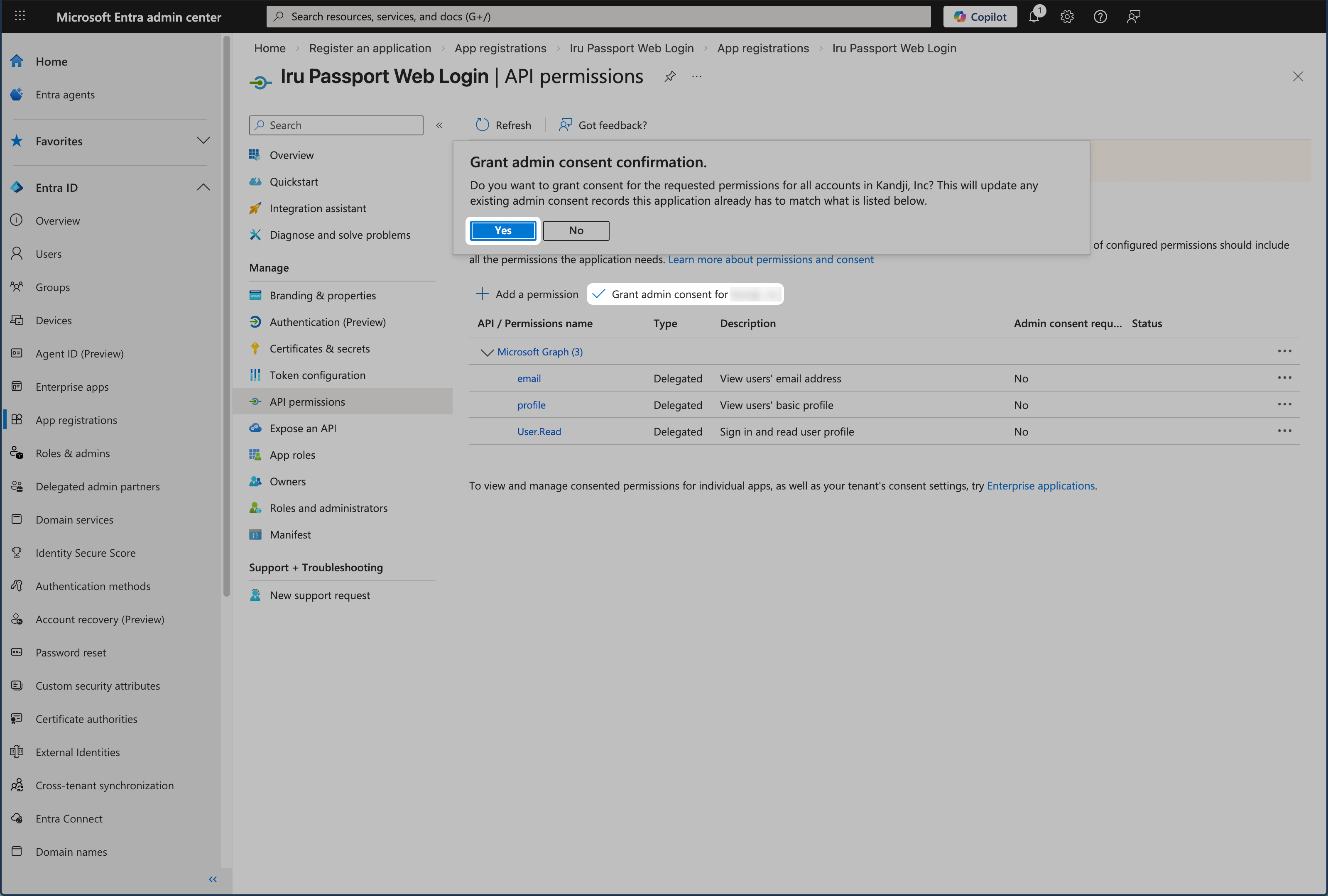
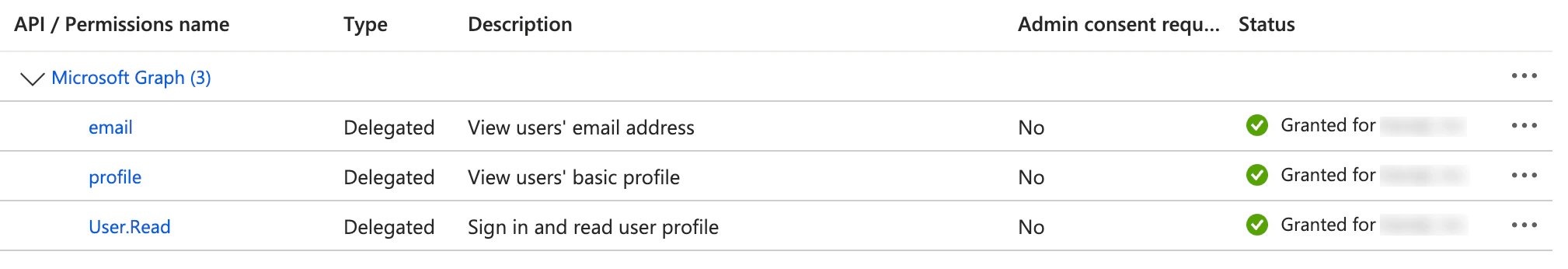
API Permissions
Add the Microsoft Graph permissions Passport needs (email, profile, User.Read) and grant admin consent so users can sign in.Expand OpenID permissions
Confirm that the OpenID permissions section is expanded. If it isn’t, click the icon next to it to expand it.
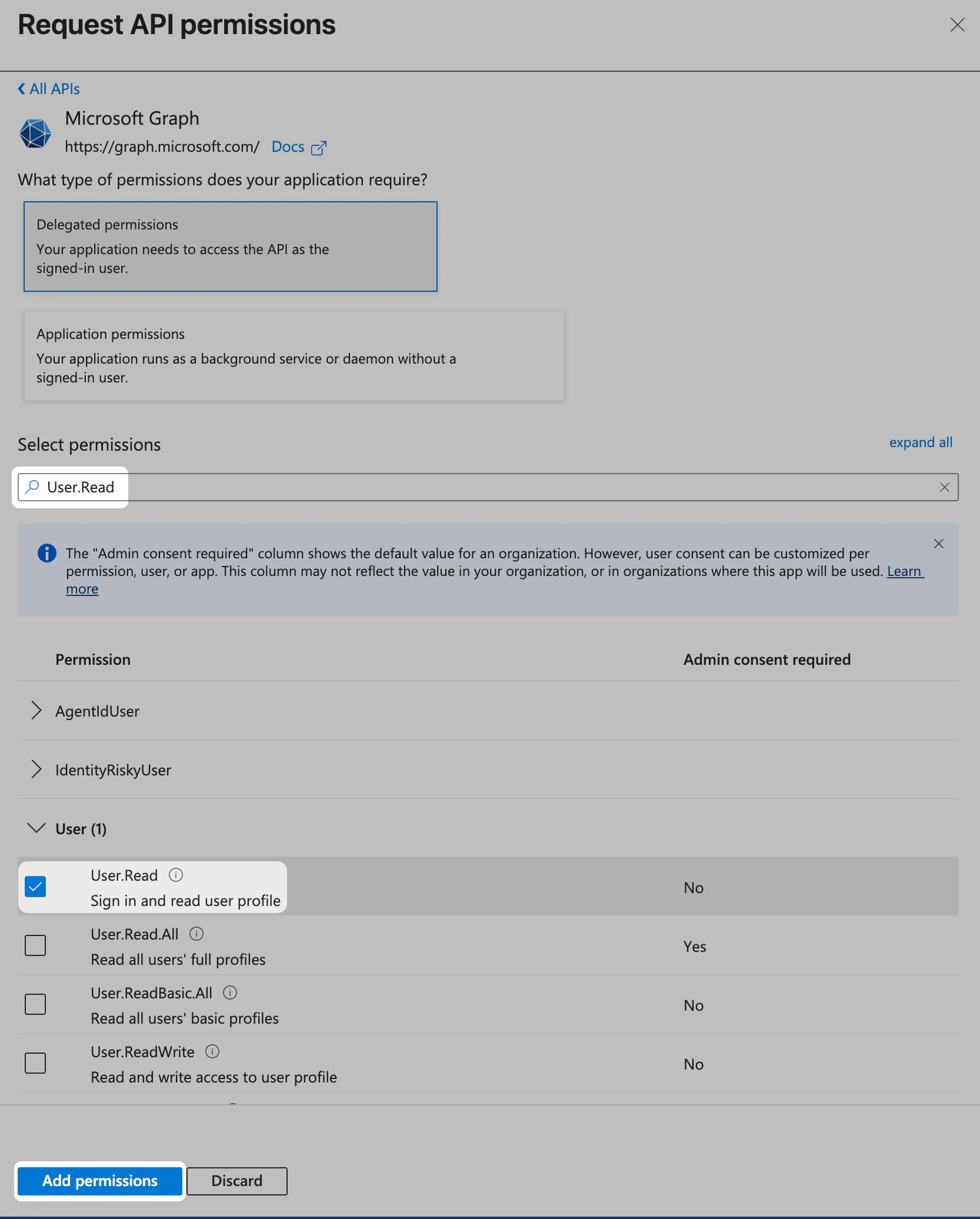
Confirm User.Read selection
In the User section, confirm that User.Read is already selected. If it isn’t, select it.
Assign Users and Groups
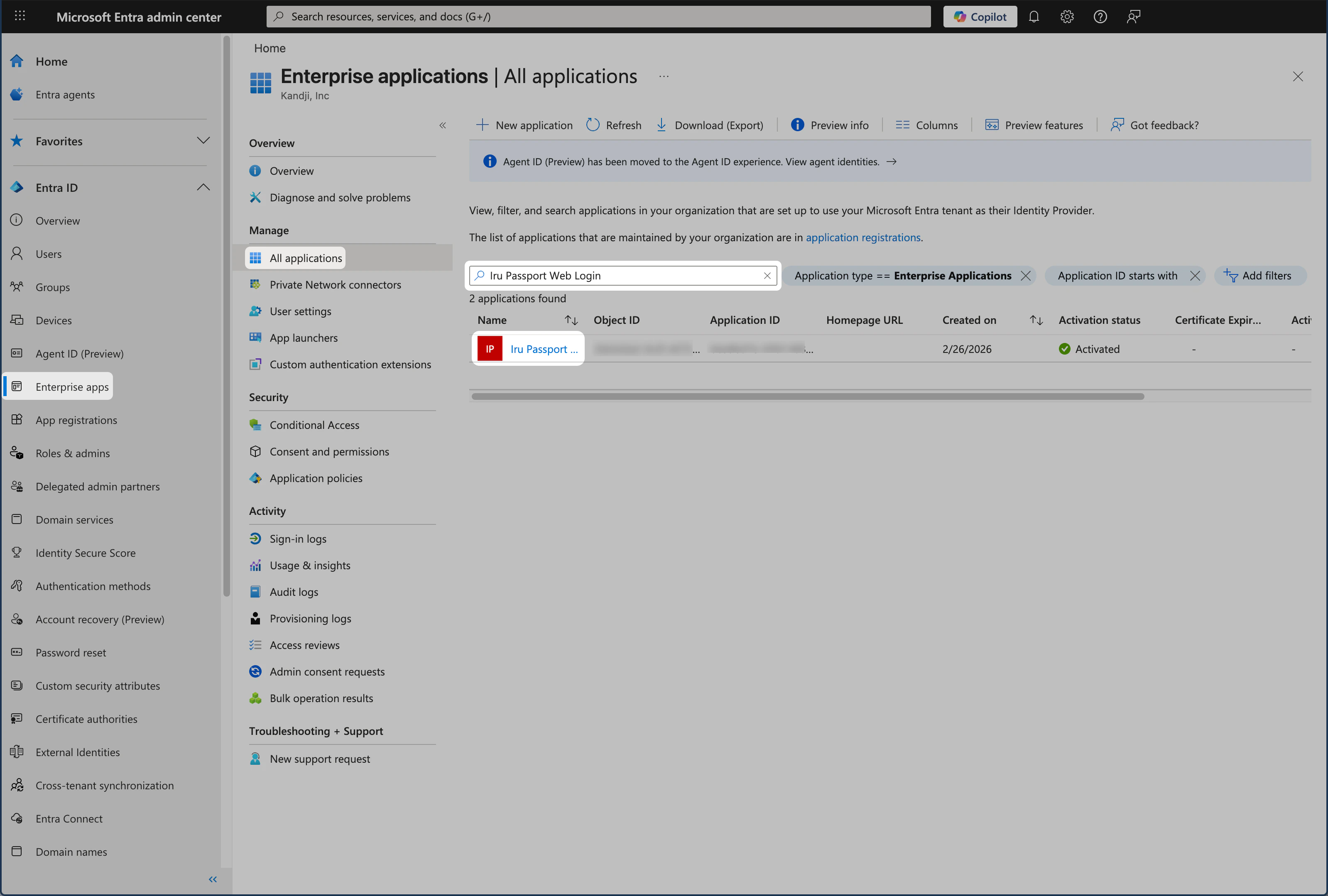
Configure who can use the Passport app and whether it appears in the user portal. By default, all users in Entra ID can use the app; the steps below cover the Properties settings and assigning users or users and groups when required.Select Passport application
In the All applications list, select Iru Passport Web Login or whatever name you gave the App registration in the previous section.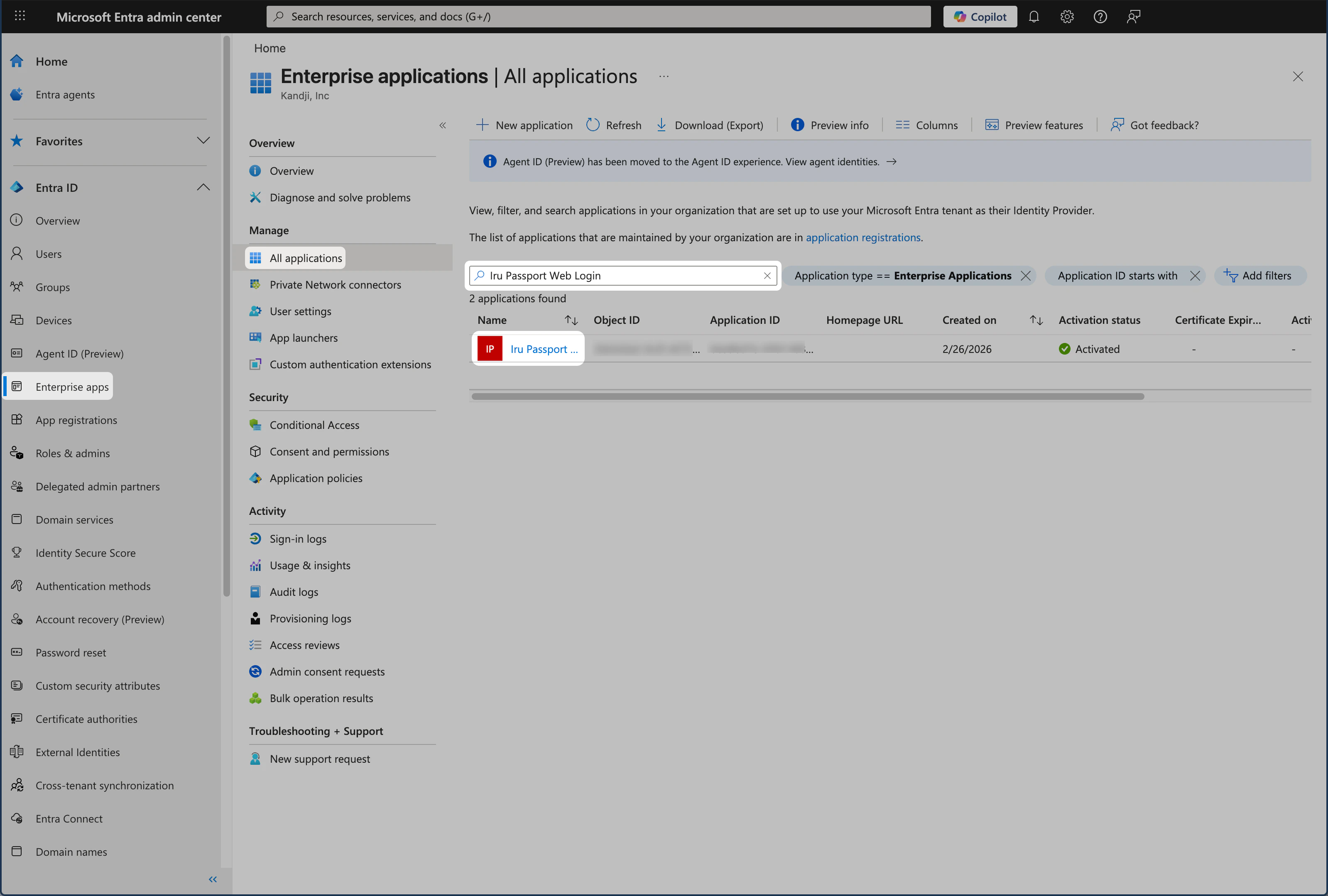
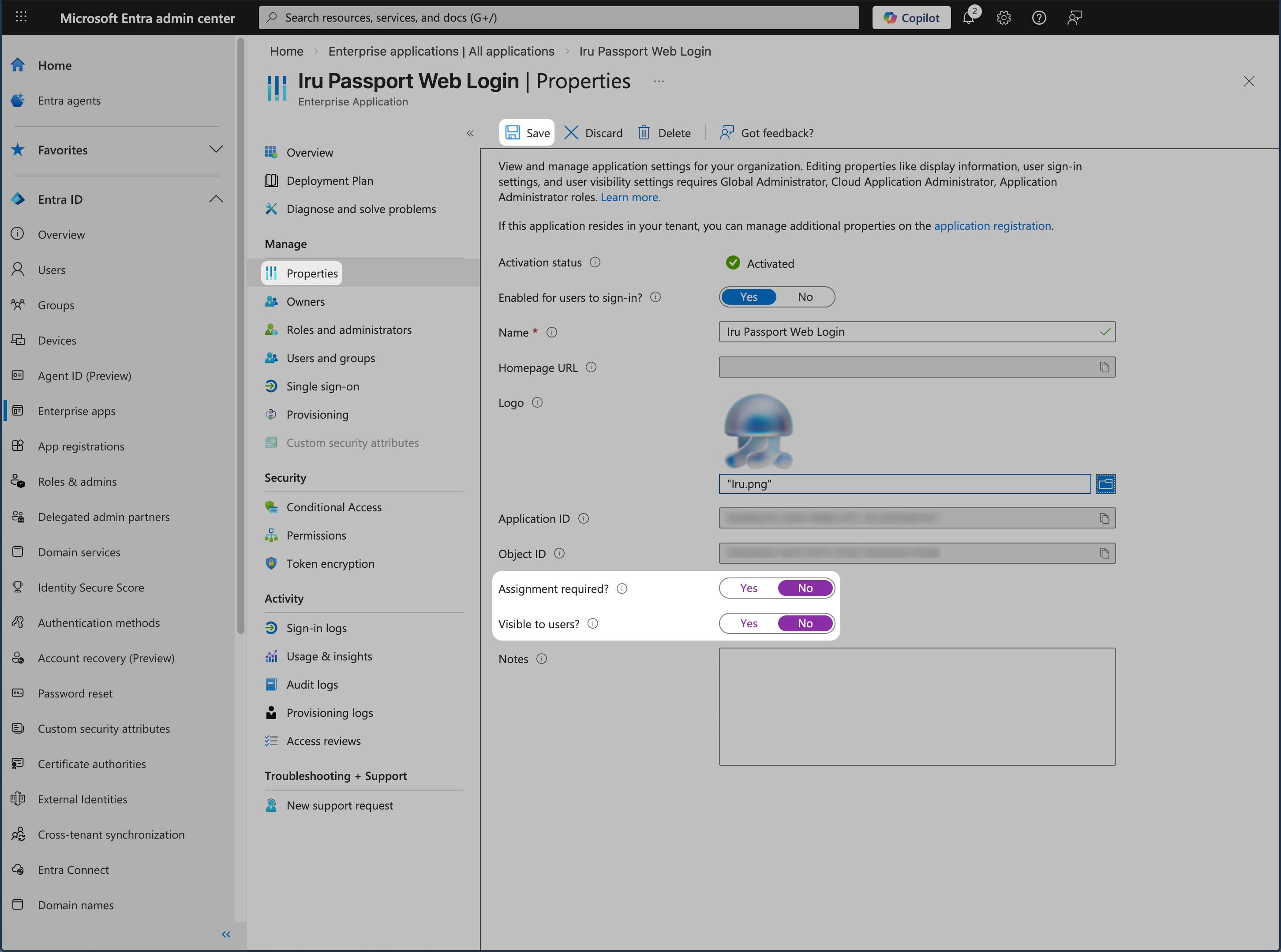
Open the Properties pane
In the left menu, under the Manage category, select Properties to open that pane.
Check assignment requirement
Inspect the Assignment required? setting:
- No: You will not need to assign users or users and groups.
- Yes: You will need to assign users or users and groups.
Configure visibility
Set Visible to users? to No.If it is Yes, users will see the app in their portal. The Passport app is only useful as a replacement for the macOS login window.
If Assignment required? is set to No, you can go directly to User Account Provisioning via Passport. If it is set to Yes, continue with the steps below.
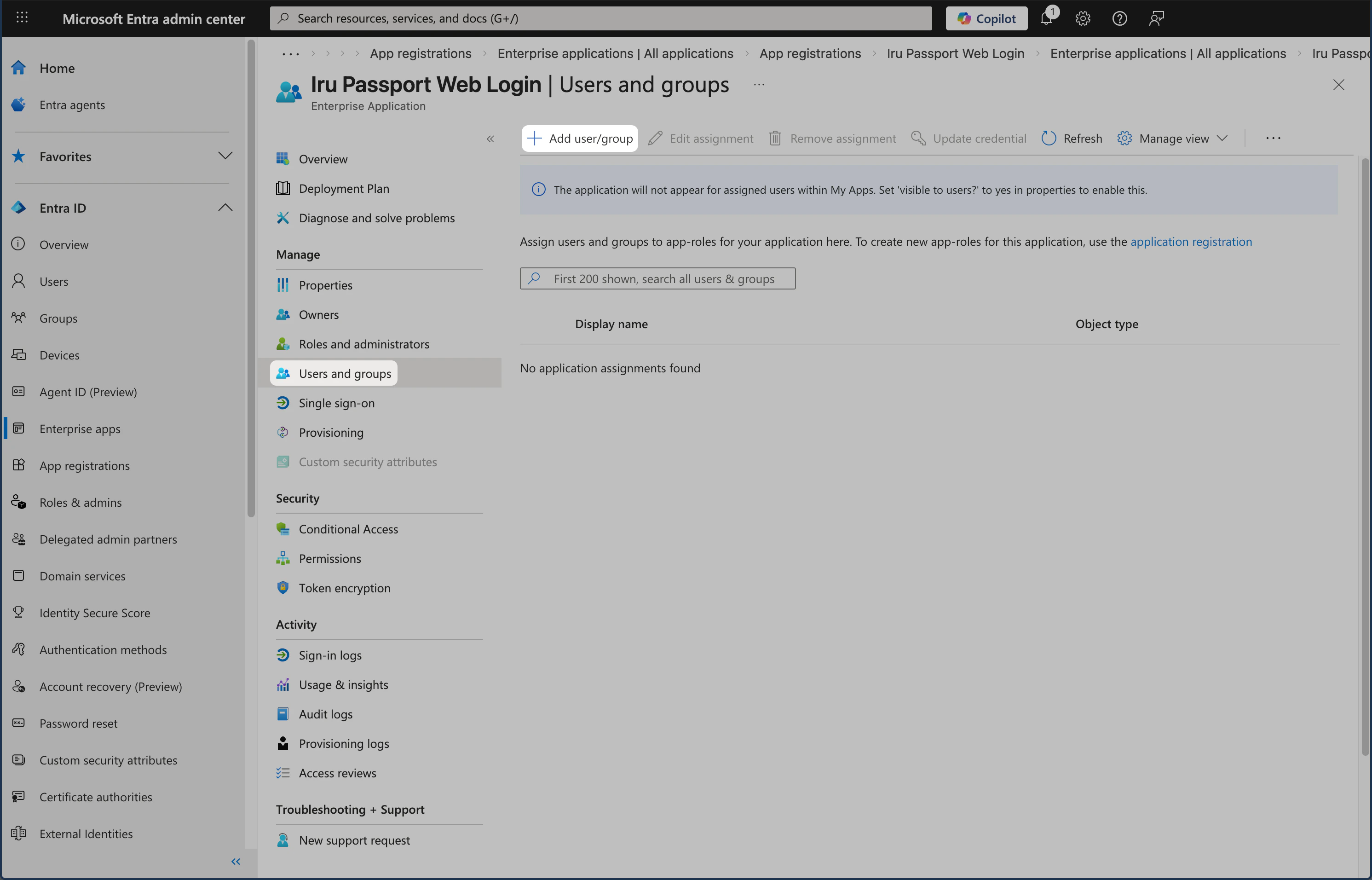
Assignment Required
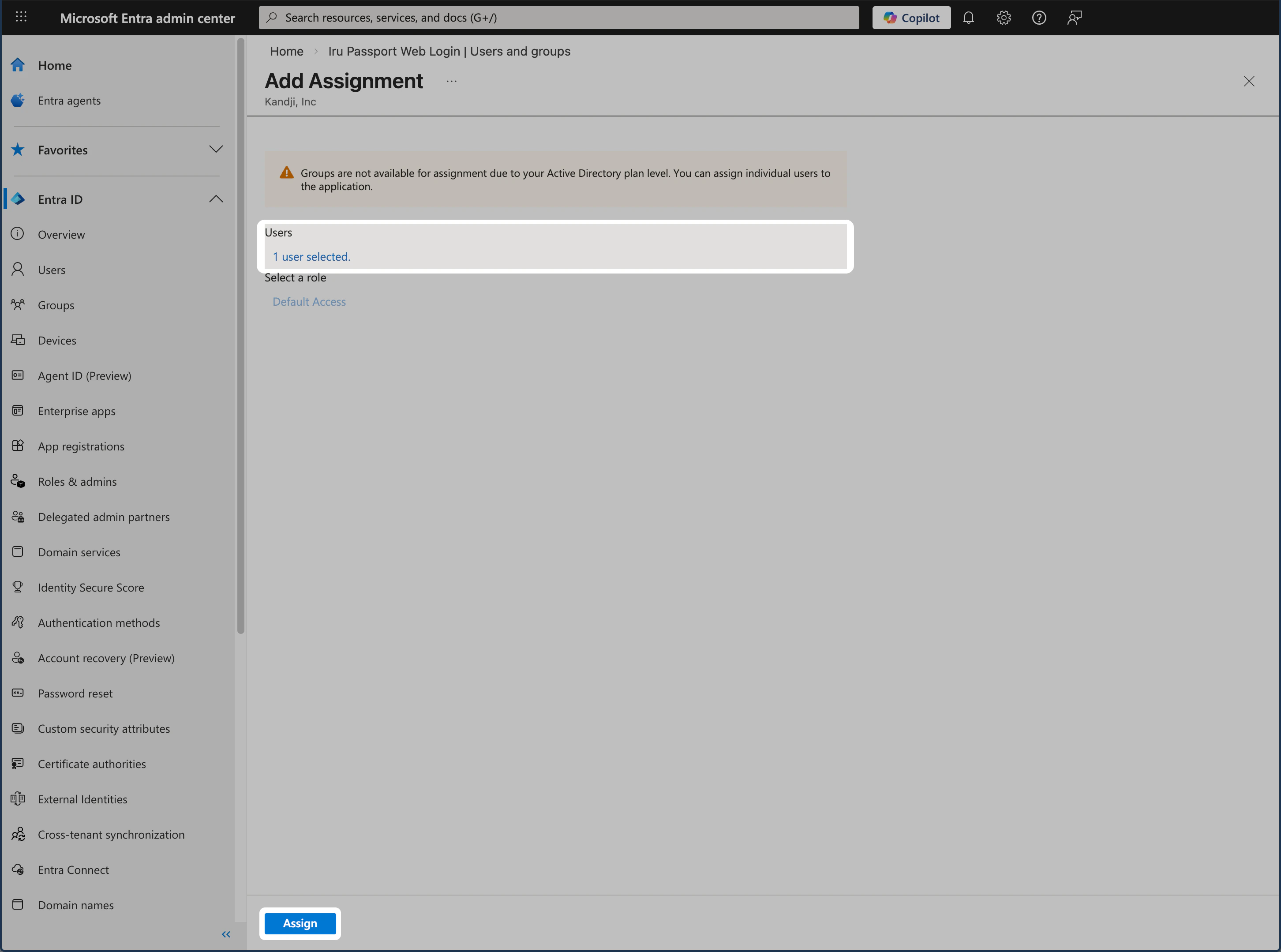
If your Passport Enterprise Application has the Assignment required? Property set to Yes, follow the steps below to assign users or users and groups.Open the Users and groups pane
In the left menu, under the Manage category, select Users and groups to open that pane.
Select users and groups
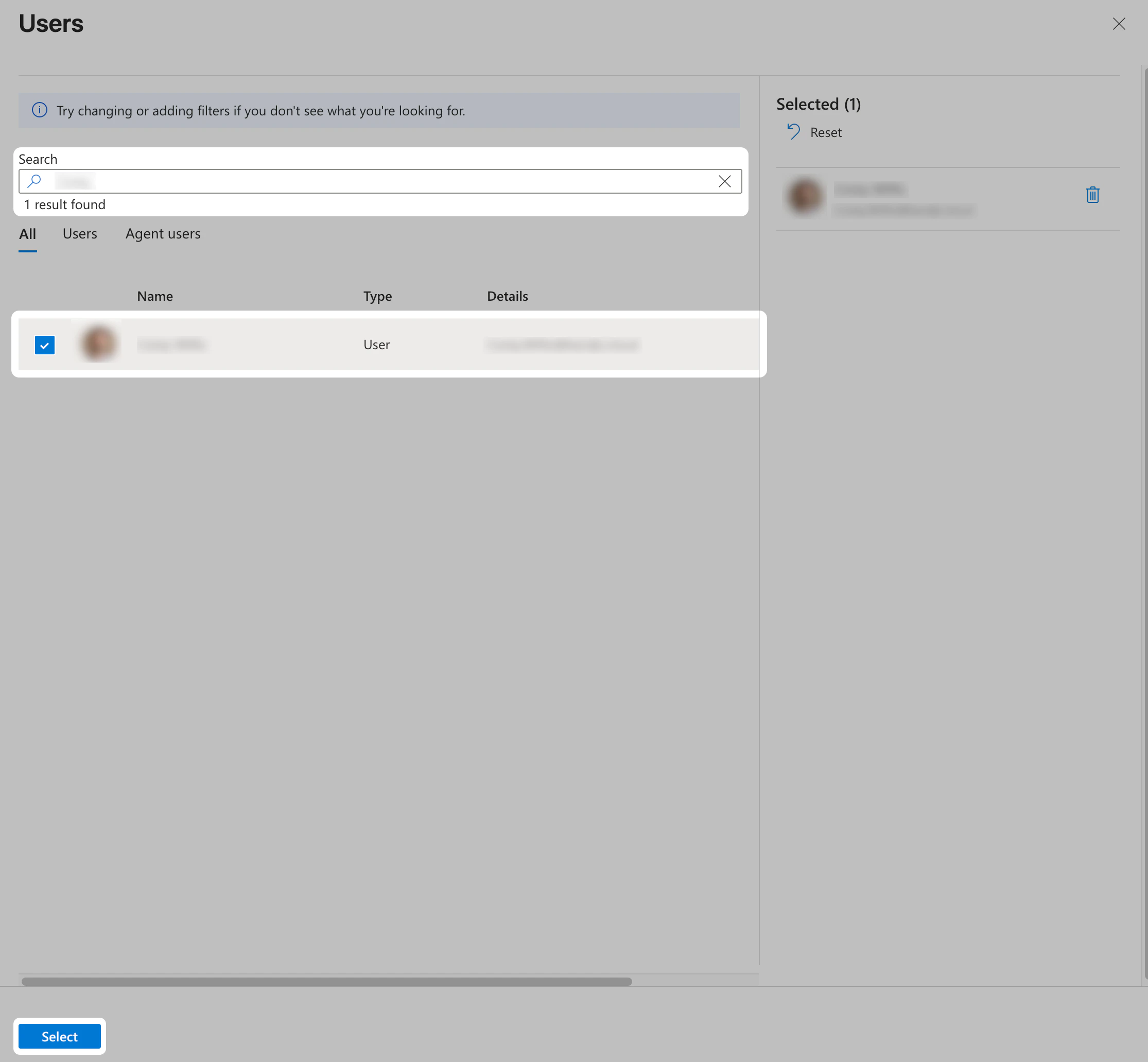
On the Add Assignment page, under the Users or Users and groups heading, select the None selected link to choose who can use the app.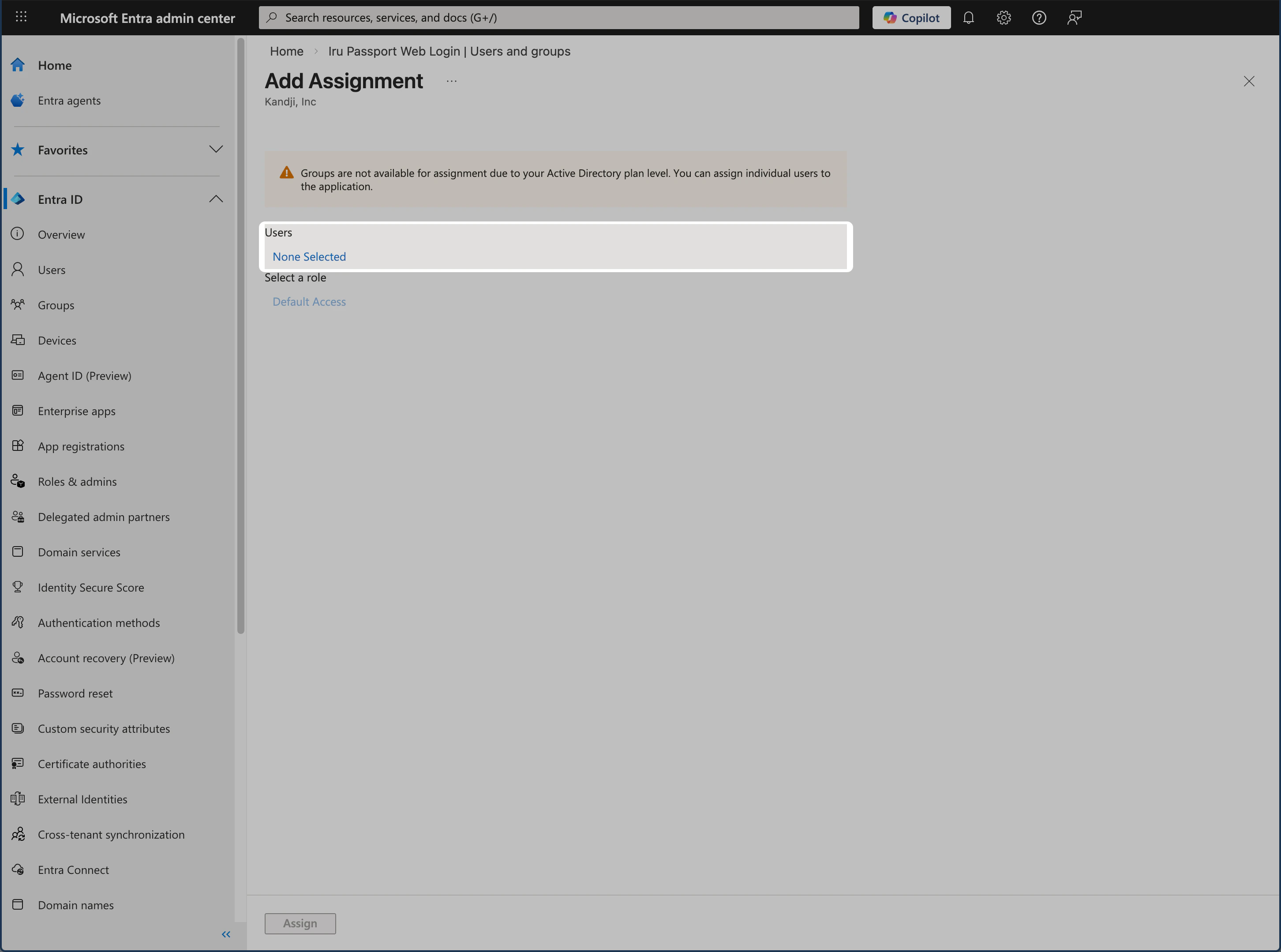
Depending on your Microsoft Entra ID plan, you may only be able to assign users, not groups. In that case, the heading shows Users and group assignment is not available.
Choose users or users and groups
A list of users or users and security groups is displayed. You can search for a specific user or group, or select multiple users or users and groups that appear in the list.
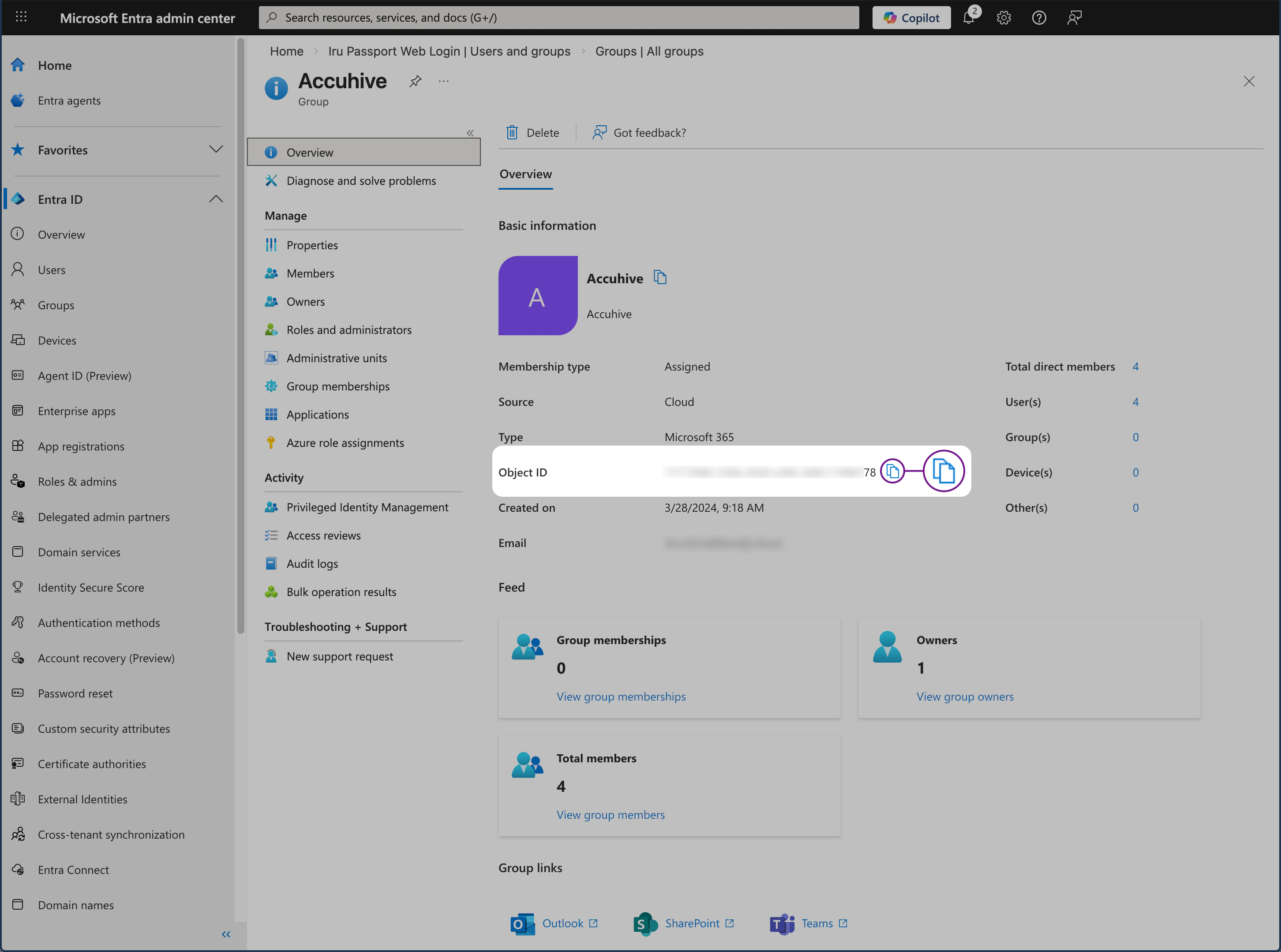
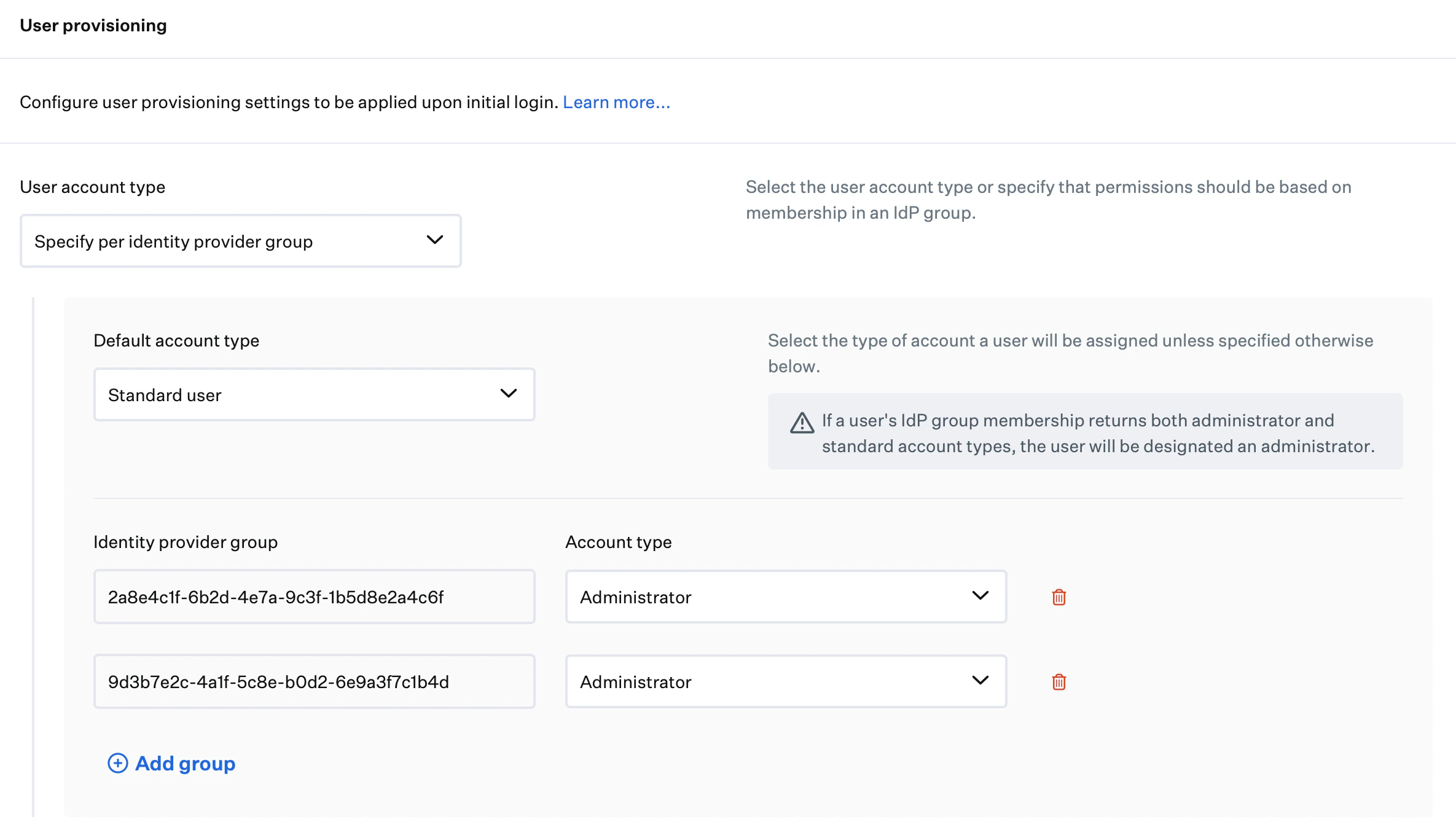
User Account Provisioning via Passport
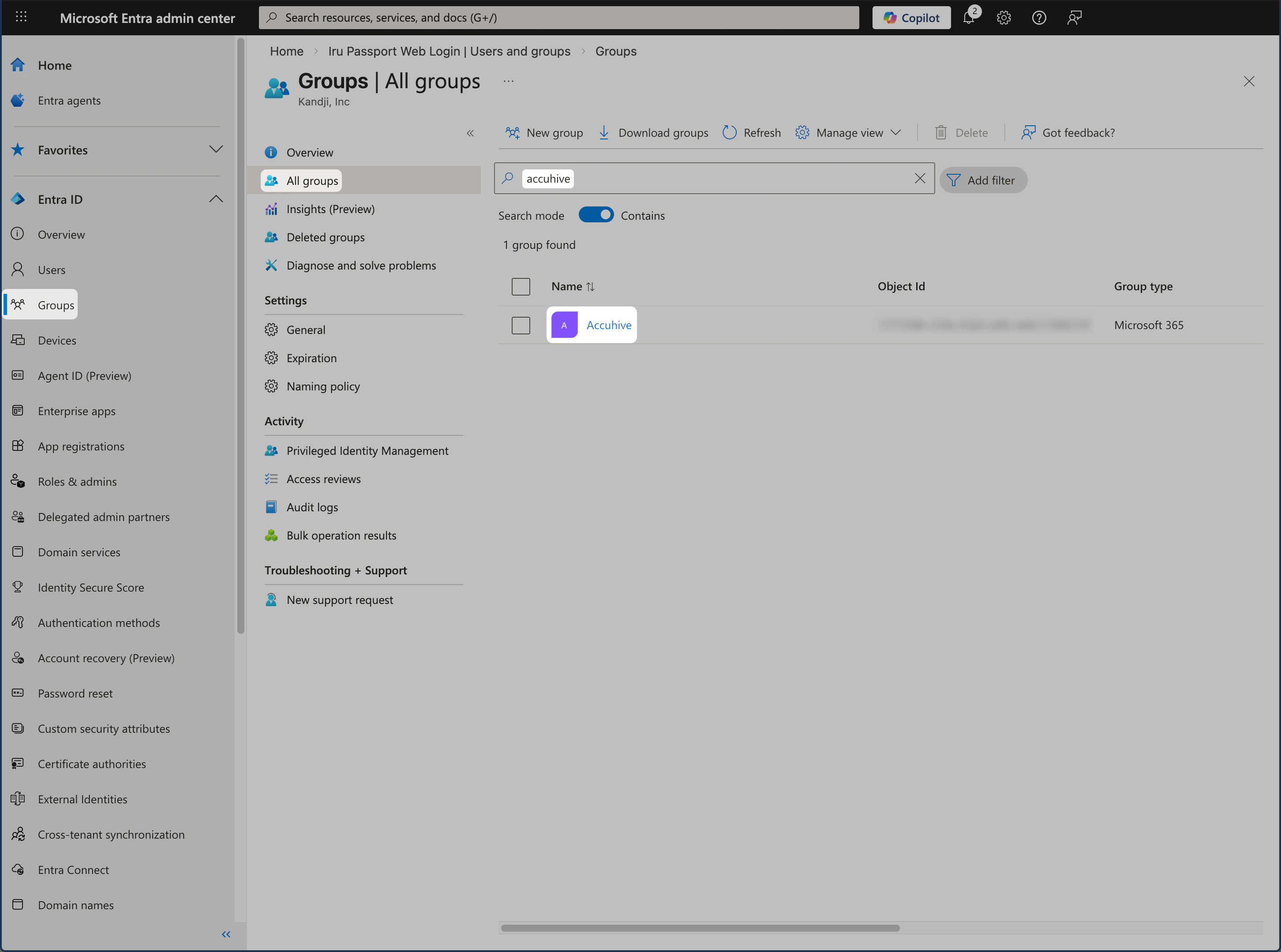
If you want Passport to set each user’s Mac account type from Entra ID security group membership, collect each group’s Object ID in the Microsoft Entra admin center using the steps in this section. You will use those values under User provisioning on the Passport Library Item Iru Endpoint tab. For more detail on this mode, see User provisioning in Configure the Passport Library Item.Access Groups
Sign in to the Microsoft Entra admin center. In the Identity navigation menu on the left, open Groups and select All groups.
Repeat for additional Entra ID groups
For each additional Entra ID group you want to use, repeat Select group and Copy Object ID. Keep the Object ID values in a secure document until you enter them on the Iru Endpoint tab.
Configure Authentication mode and User provisioning in the Passport Library Item on the Iru Endpoint tab.