Documentation Index
Fetch the complete documentation index at: https://docs.iru.com/llms.txt
Use this file to discover all available pages before exploring further.
About Passport
Passport is a feature in Iru Endpoint that allows users to log into Mac computers using their organization’s Identity Provider (IdP) credentials instead of separate local passwords. This streamlines authentication by connecting your IdP directly to macOS login.How It Works
Passport integrates with your Identity Provider (IdP) to authenticate users at the macOS login screen. When users enter their IdP credentials, Passport verifies them against your organization’s identity system and creates or updates the local Mac user account accordingly. For more information about how Passport interacts with other Iru Endpoint and macOS features, see Passport Compatibility with macOS & Iru Endpoint Features.Set Up Your IdP for Passport
Set up your identity provider with Passport before you configure the Library Item in Iru Endpoint. Depending on your IdP and authentication mode, you will need the right values to enter in Iru Endpoint, such as the OIDC well-known configuration URL (issuer metadata URL), the application client ID, and, when your setup requires them, client secrets and redirect URIs. Use the guide that matches your IdP:Passport Configuration with Google Workspace
Passport Configuration with Okta
Configure Passport with Microsoft Entra ID - Web Login
Configure Passport with Microsoft Entra ID - Mac Login
Passport Configuration with OneLogin
.well-known/openid-configuration URL and the client settings that match Web Login or Mac Login in your Passport Library Item.
Create a Passport Library Item
Add Library Item
Configure name and Blueprints
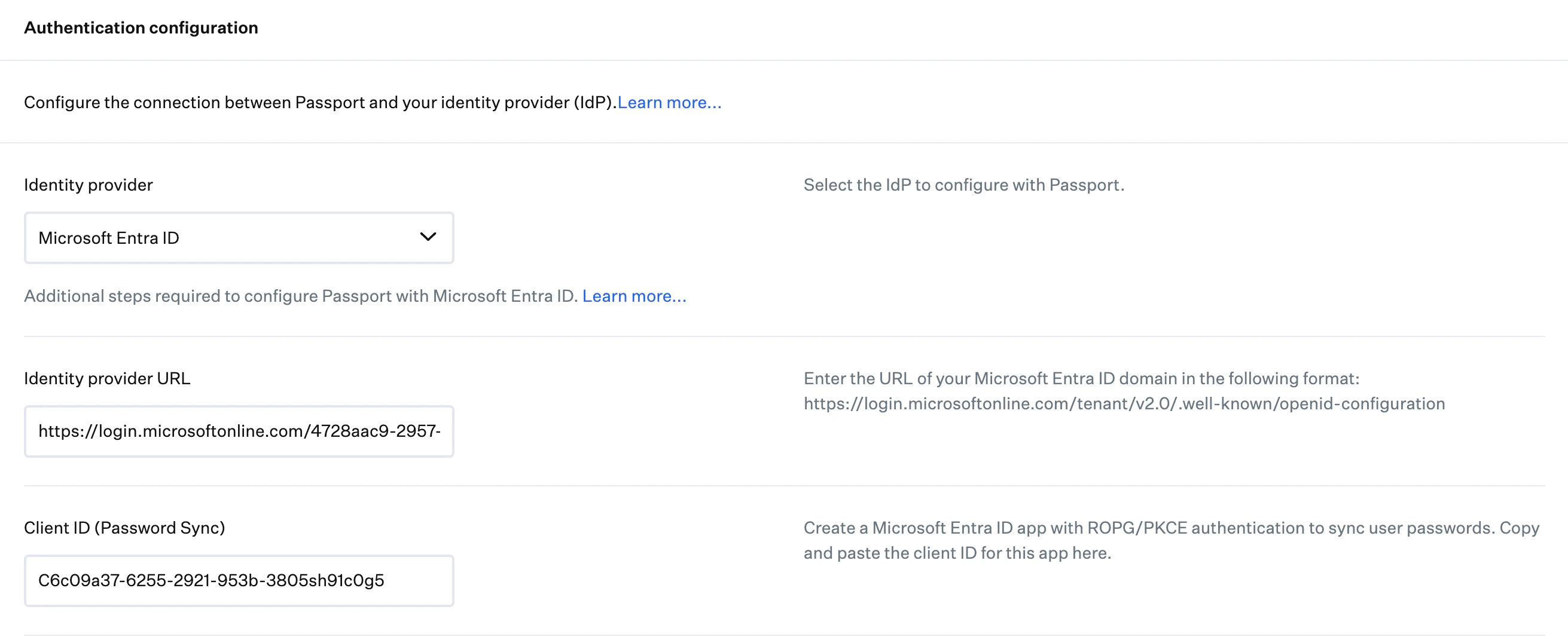
Authentication Configuration
Select Identity Provider
Google Workspace: upload certificate
Enter Identity provider URL
- Microsoft Entra ID
- Okta
- OneLogin
- Other
Enter Client ID (Password Sync)
Select Authentication mode
- Web Login: Passport shows a web view of your IdP’s sign-in page. Users complete IdP sign-in (including multifactor authentication when your IdP requires it) inside that view. When your organization allows it, they can sign in locally.
- Mac Login: Passport shows the Mac username and password fields only. Users enter their IdP credentials there; Passport checks them against the IdP without running the IdP’s full web sign-in flow at the login window.
Configure Redirect URI (if applicable)
Enter Client secret (if applicable)
User Provisioning
Configure the user provisioning settings you want to be applied when a user first logs in to the Mac. You can control how account types are assigned and what to do when an account already exists.How Passport links IdP users to local accounts
How Passport links IdP users to local accounts
dscl command or the Directory Utility app):dsAttrTypeNative:io.kandji.KandjiLogin.LinkedAccount: contains a unique value specific to the IdP account; this varies and could be a number, email address, or unique identifierdsAttrTypeNative:io.kandji.KandjiLogin.LinkedAccountName: contains a value from the RecordName attribute of the linked user account, for example, an email address
User account type
User account type
- If you select Administrator or Standard, Passport checks a local account’s permissions at the initial Passport login.
-
If you select Specify per identity provider group to configure the new account type based on IdP group membership:
- With User account type set to Specify per identity provider group, open the account type drop-down below it and select Administrator or Standard user. If a user matches an Identity provider group row farther down, Passport uses that row’s account type instead.
-
Ensure the group in the Identity provider group field in Iru Endpoint matches the group in your IdP
- For Microsoft Entra ID, based on Microsoft’s recommendations, use the Entra ID group Object ID instead of the group name.
- For Google Workspace, the name entered should be the email prefix of the group in Google as opposed to the name of the group.
- If a user is designated as an administrator in one group and a standard user in another, that user’s account type will be Administrator.
-
When Specify per identity provider group is selected, Passport checks the user’s group membership every time the user logs in. Passport updates the user’s account type if you make a group membership change or a configuration change that would cause a user to:
- change from a standard account to an administrator account
- change from an administrator account to a standard account (this change forces the user to restart their Mac to demote the user account and ensure that the change is in effect)
Ask to link account with a local user
Ask to link account with a local user
-
Always. This is the default setting. When a user logs in to the Mac using their IdP credentials, Passport will prompt the user to select an existing local Mac account they want to link to. It is a good option if you are unsure whether or not your users’ IdP account names match their Mac account names. When Always is selected, you will see two additional options:
- Require linking to an existing local user: The user will be required to link their IdP account to an existing local user account.
- Exclude local users: Exclude specific accounts from the list of local users able to be linked during the user’s initial login. Enter a short name in Local user short name and select Add user when you need more than one row. A common use case is preventing the user from being prompted to link an IT admin or service account.
- If a local username matches. When a user logs in to the Mac using their IdP credentials, Passport will automatically find the Mac account with a matching username and prompt the user to link it. The user will not have the option to link to another account.
- Never. When a user logs in using their IdP credentials, Passport will create a new user account on the Mac, regardless of existing accounts.
Access
Configure which users can log into the Mac and FileVault’s automatic login behavior. Our Managing Passwords with Passport article provides in-depth information regarding password management using Passport.IdP user access
IdP user access
- Allow all users to log in allows all IdP users to log into the Mac at the Passport login window.
-
Specify which IdP users can log in allows only users you specify to log into the Mac at the Passport login window.
- Automatically include user assigned to device record: Automatically allows the user assigned to the device record in Iru Endpoint to log in.
- Specify additional IdP users: Allows certain IdP users to log in, even if they aren’t assigned to the device record in Iru Endpoint.
Local user access
Local user access
- Allow all local users to log in allows all local users to log in to the Mac at the Passport login window. If the Mac is connected to a network and can reach the IdP, Passport will check the user’s credentials against the IdP. If the Mac is not connected to a network, the user can log in with their local Mac account credentials. This is the default setting.
- Allow local administrators to log in allows only local administrator users to log in to the Mac at the Passport login window.
- Specify which local users can log in allows only users you specify to log into the Mac at the Passport login window.
Automatic FileVault login
Automatic FileVault login
- Allow automatic FileVault login: Users sign in only at the FileVault login window. They do not see the Passport login window unless they log out. The FileVault login window does not check credentials against an IdP.
- Disallow automatic FileVault login: This is the default. Users see the Passport login window when they turn on their Mac. They sign in at the FileVault login window and again at the Passport login window.
Store user password
Store user password
-
Securely store password: Stores the user’s IdP credentials in a dedicated keychain on their Mac to aid in password changes. When the user changes their password with their IdP and then logs in to the Mac, they only need to enter their new credentials; Passport will silently update the Mac password. If a user is already logged in and changes their password with the IdP, Passport will prompt them within 5 minutes to update their local password, and the user will not have to provide their local password; they will only have to enter their IdP password for Passport to change their local password to match their IdP password. The location of this keychain is
/Library/Keychains/iru.keychain. If you remove that keychain, Passport will automatically create a new keychain in that location and use it without generating an error or notification to the user.- Web Login Passthrough: When this option is selected with Web Login, users will see an additional password verification screen only the first time they log in. The login process will be completed after a single authentication at the Web Login window on subsequent logins.
- Do not store password: With this option set, Passport only checks and enforces password synchronization at login. If a user changes their password in between login sessions, their local password will remain out of sync until their next login.
Customize Login Window
You can customize the Passport login window for your users. Click Customize to reveal the Customize login window drawer with the following options:Branding
Branding
- Display logo: Include your organization’s logo on the login window. If the Passport Library Item uses Web Login, Passport shows the web view instead of the logo until the user selects Local Login, which brings back the logo with the username and password fields.
- Logo: Use a 128 x 128 pixel PNG with a transparent background. Drag the file into the upload area or select upload. JPEG and PNG are accepted.
- Customize Desktop picture: Turn this on to upload a picture for the login window background.
- Desktop picture: A 3840 x 2160 pixel JPEG or PNG is recommended. Drag the file into the upload area or select upload.
Menu bar
Menu bar
Banners
Banners
Power controls
Power controls
- Shut Down button
- Restart button
- Sleep button
Username and Password
Username and Password
- Customize username label: Add a custom label that appears in the username field. Up to 83 characters.
-
Include password reset URL: Allow users to reset their passwords from the login window. Enter the full URL, for example a value starting with
https://.
Customize Help Window
Users select the Help ? control in the bottom left of the Passport login window. The Help window that opens has three tabs across the top: Support, Device info, and About, matching what you configure here. In the Passport Library Item, click Customize to open the Customize Help window drawer.Support tab
Support tab
- Header: Required. Up to 30 characters. This text appears as the main heading on the Support tab, for example Contact us.
- Body text (optional): Up to 250 characters. This text appears under the heading, for example instructions to contact the organization’s IT department if login fails.
Device info tab
Device info tab
- Serial number
- IP address
- Hostname
- macOS version
- Model information
About tab
About tab





